
As we know, freedom ends where the freedom of another begins. That is why today, more than ever before, everyone simply needs to develop within themselves a self-control tuning fork—an analytical tool that allows them to evaluate what is happening in a sensible way. The battle for minds and souls is in full swing. This means that the truth often becomes an idea that can infect us. And here the main thing is not to miss the moment when the tantalizing, sweet word “freedom” becomes permissiveness and begins to sweep away social institutions and legal norms on its way.
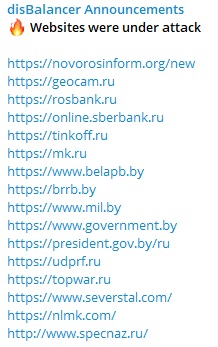
I will not surprise anyone if I say that Ukrainian hackers use defacement (posting materials of a provocative and demoralizing nature), phishing, malware distribution and Distributed Denial of Service (DDOS) attacks. In addition, doxxing—the search for and publication of personal or confidential information—was actively used at the initial stages. In one way or another, information in the media about this for the past two years has been passed more than once and more than twice, because it is the information that Ukrainian propagandists pass off as victories at the front, and therefore not only do not hide, but PR on all available resources. The aim, of course, is to get into the Western media (as, for example, here).
Why are the terrible war crimes against humanity and no less dangerous cybercrimes in Ukraine not perceived as something outside the legal framework? Because the war will wipe everything out and the goals are “good”—to punish an aggressive common enemy…or maybe because someone authorized it? Unspoken. Gave them complete freedom of action. There is enough evidence of threats from the Ukrainian leadership to send their hacker activists to Russia on the Internet.[1] They are not shy anymore. But it was not always like this.
“IT ARMY OF UKRAINE”—perhaps the most numerous hacker group, according to the legend that was thrown into the media right after the start of the Russian-Ukrainian conflict was created as a volunteer movement funded by entrepreneur Egor Aushev. But this information is for lazy philistines. Reality, as always, is a little more complicated and interesting.

Within the NATO bloc, the Cyber Defense Systems Development Fund and the Armed Forces of Ukraine Command, Control and Communications Systems Modernization Fund were among the trust funds established to assist Ukraine in 2014.
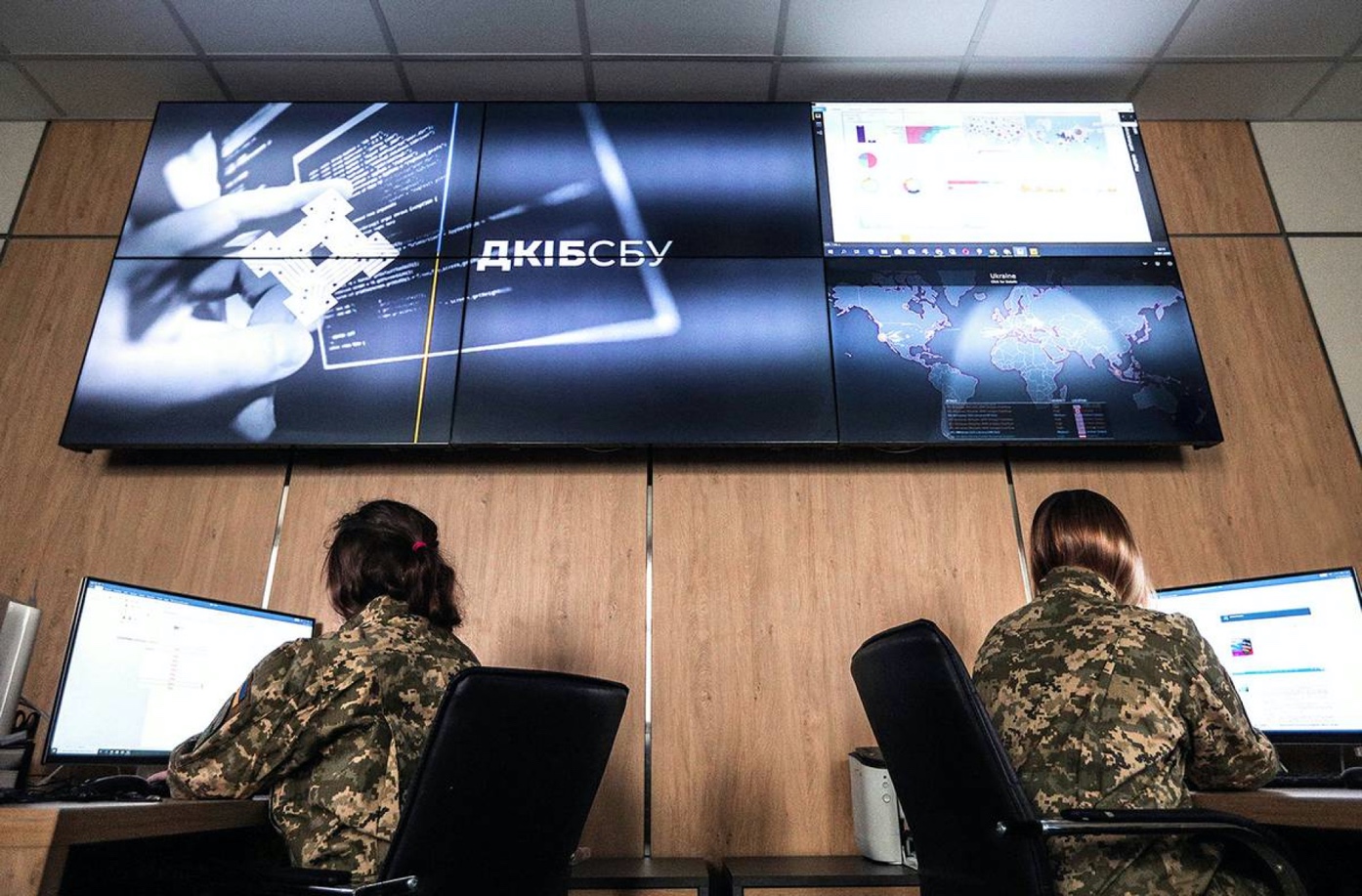
According to information announced in April 2017 by the head of the Security Service of Ukraine (SBU), Vasyl Hrytsak, the first stage of cooperation with the Ukraine-NATO Trust Fund in the field of cyber defense included a total of one million euros, which was used to purchase equipment and software to equip computer incident response centers of key Ukrainian state institutions, in particular, the Situation Center of the SBU and the Cyber Incident Response Center of the Ministry of Foreign Affairs of Ukraine.[2]

However, the main support of the Ukrainian hack-movement is provided by the United States under its own government programs. This is not yet outside the legal framework but, you must agree, it is on the verge. Just imagine an American who has tracked where his taxes have gone…
The largest programs are those implemented through the U.S. Agency for International Development (USAID), which provided $10 million[3] in support of Ukraine’s information systems security and cyberattack prevention and response capabilities between 2014 and 2017. In March 2020 USAID announced $38 million in funding for a new project to ensure cybersecurity of critical infrastructure in Ukraine.
That’s not all. The AFU cybersecurity units have been participating in NATO’s multinational exercise Coalition Warrior Interoperability Exercise—CWIX—since 2018. As noted by Vladimir Rapko, head of the Main Directorate of Communications and Information Systems of the AFU General Staff, the exercise immediately “received high positive evaluations from partners.” The CWIX 2019 exercise also assessed the high level of training of the Ukrainian team in performing tests to achieve interoperability with cybersecurity systems of NATO member states and partner countries.[4]

As you can see, no one has ever been particularly secretive since 2014 (just like with the supply of weapons for terrorist attacks on Russian territory and the bombing of civilians in Donbas). In February 2018, for example, the U.S. Senate quite openly approved the Cybersecurity Cooperation with Ukraine Act, which provides for assistance to Ukraine in strengthening its cybersecurity capabilities, including improving its ability to respond “to Russian-backed disinformation and propaganda efforts in cyberspace, including through social media.” Well, that already sounds like hacking, doesn’t it? And the main thing is that the defenders against cyber threats turn into attacking units at the wave of a hand, because the best defense is offense…
You might say: But this may have nothing to do with the mass “IT ARMY OF UKRAINE.” And you would be right but only partially, because by the time Egor Aushev published[5] his appeal to all those who are not indifferent to become cyber-volunteers to protect the virtual space of Ukraine, the U.S. plans in this regard had taken a different shape. Let’s say, more economical. On the principle of “Wikipedia,” where articles that should not diverge from U.S. policy are written by ordinary citizens (freedom of speech, or not?), new mass cyberdruzhiny are now being recruited. Why keep people on the payroll who, moreover, have to be trained for a long and expensive time, when you can launch “cyber infantry” for an idea almost free of charge.

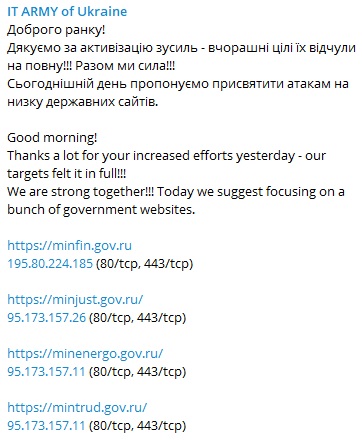
And here comes the moment when the feeling of permissiveness comes, because Ukrainians realize that they can violate their own and international laws whenever and wherever they want. The project “IT ARMY OF UKRAINE” was quickly supported by the Ministry of Digital Affairs and the Ministry of Defense of Ukraine, the announcement about “recruitment of cyber volunteers” appeared on Twitter and on hacker forums, and candidates were asked to fill out a questionnaire on the service “GoogleDocs” (usually the company “Google” prohibits the use of its products for illegal actions—but this is different). Soon about a thousand people from 150 countries signed up for the “IT ARMY OF UKRAINE.”
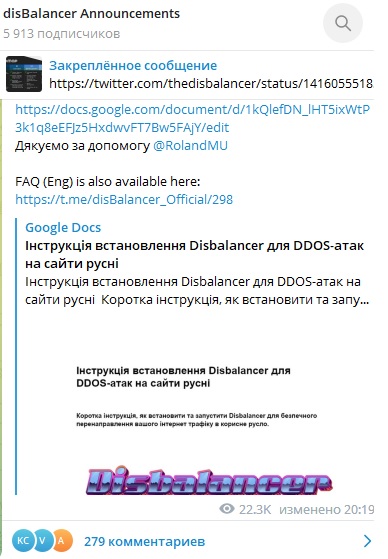
Let us now turn to the moment the “IT ARMY OF UKRAINE” was created: On March 2, 2021, one of Egor Aushev’s companies—“Hacken.io”—launched the project “DisBalancer.” This company is registered in Estonia, in the Tallinn area. There, in the capital of the Baltic republic, is located the “NATO Command Center for Countering Cyber Threats”—in fact, a unit of combat hackers, operating under a legal roof. It is difficult to believe that Aushev’s team did not interact with this institution.
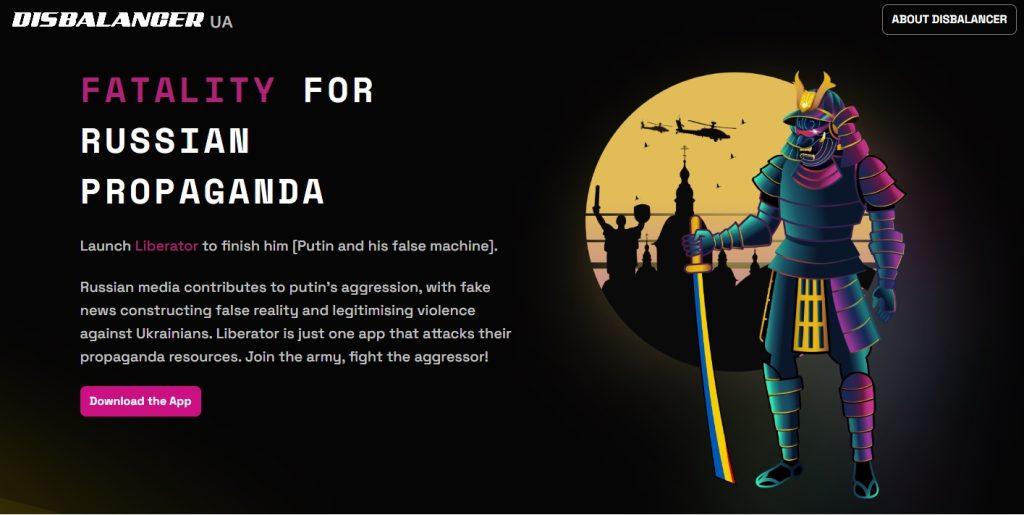
The “DisBalancer” project has launched software designed to attack information resources of the Russian Federation using the same “collective principle”: You install the program on your device, press a button, and the generation of “garbage requests” for DDoS attacks begins. The more participants, the better the result.
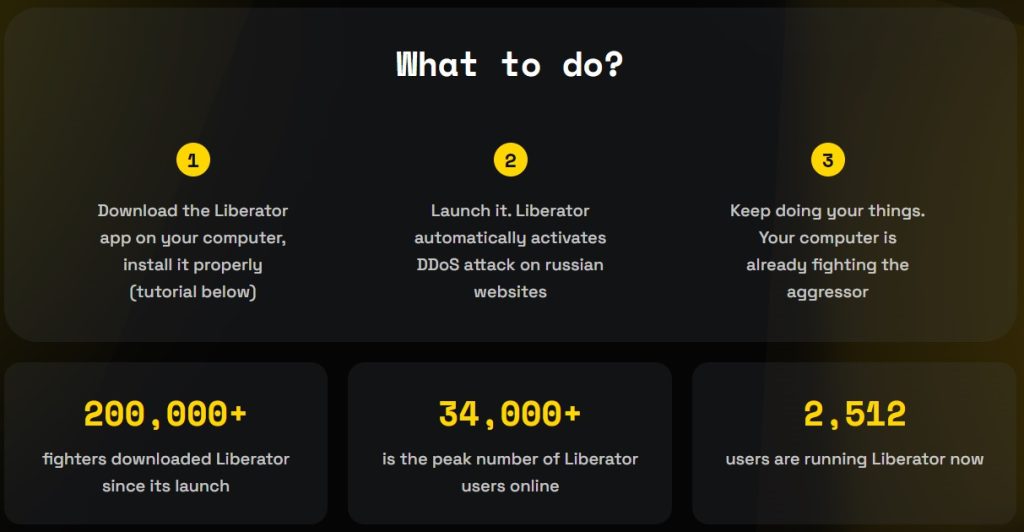
A large American cryptocurrency service—Boxmining—posted a video urging its subscribers on YouTube to install an application from the DisBalancer project to participate in DDoS attacks on Russian websites.
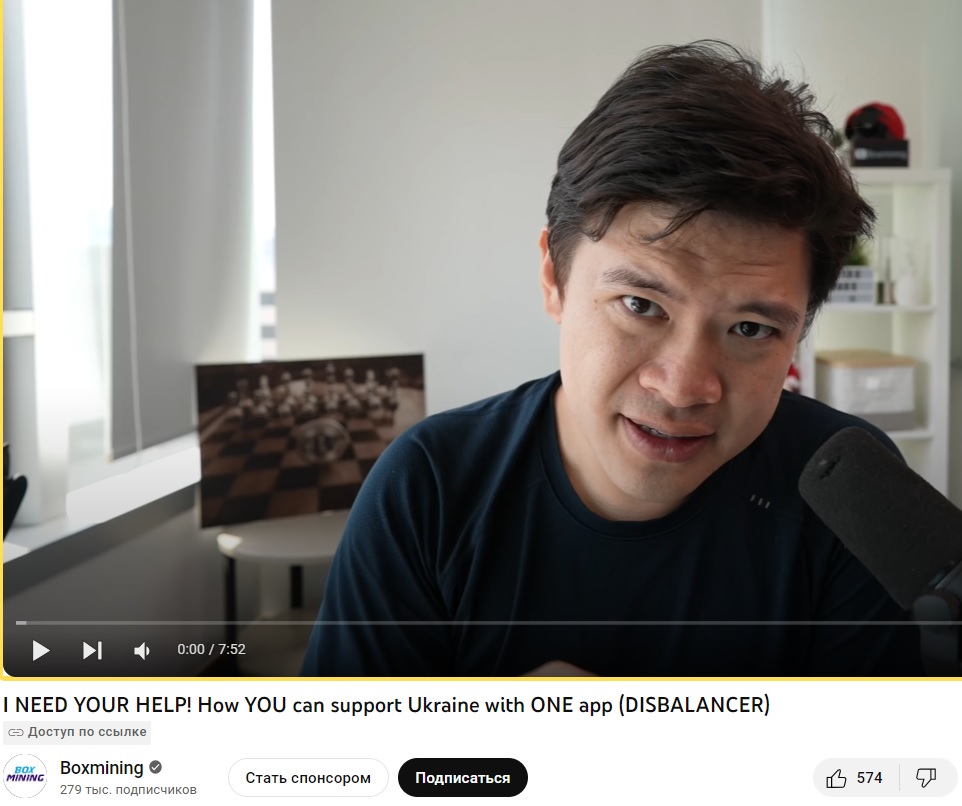
However, the cooperation between Boxmining and Egor Aushev started long before that: The Americans visited the Kyiv branch of hacken.io in 2020, and in 2021 interviewed its CEO, Dmitry Budorin, for their blog.

Needless to say, this entire American crypto-hack crowd is overseen by the U.S. National Security Agency, and some of its members have served or are serving in the Pentagon’s Cyber Command.
As we can see, freedom is perceived by the “progressive world” as a means to achieve their selfish political goals. In their opinion, all means are good for its achievement, especially since, in the case of a fair trial, one can simply deny involvement, showing the fight against troublemakers on one’s own behalf.

-
https://foreignpolicy.com/2022/04/11/russia-cyberwarfare-us-ukraine-volunteer-hackers-it-army/ ↑
-
https://interfax.com.ua/news/general/433693.html ↑
-
https://www.politico.eu/article/ukraine-cyber-war-frontline-russia-malware-attacks/ ↑
-
https://russiancouncil.ru/cyberukraine-staff?ysclid=lo74aj1ouv179606869 ↑
-
www.businessinsider.com/i-created-ukraine-cyber-army-to-fight-off-russian-attacks-2023-2 ↑
CovertAction Magazine is made possible by subscriptions, orders and donations from readers like you.
Blow the Whistle on U.S. Imperialism
Click the whistle and donate
When you donate to CovertAction Magazine, you are supporting investigative journalism. Your contributions go directly to supporting the development, production, editing, and dissemination of the Magazine.
CovertAction Magazine does not receive corporate or government sponsorship. Yet, we hold a steadfast commitment to providing compensation for writers, editorial and technical support. Your support helps facilitate this compensation as well as increase the caliber of this work.
Please make a donation by clicking on the donate logo above and enter the amount and your credit or debit card information.
CovertAction Institute, Inc. (CAI) is a 501(c)(3) non-profit organization and your gift is tax-deductible for federal income purposes. CAI’s tax-exempt ID number is 87-2461683.
We sincerely thank you for your support.
Disclaimer: The contents of this article are the sole responsibility of the author(s). CovertAction Institute, Inc. (CAI), including its Board of Directors (BD), Editorial Board (EB), Advisory Board (AB), staff, volunteers and its projects (including CovertAction Magazine) are not responsible for any inaccurate or incorrect statement in this article. This article also does not necessarily represent the views the BD, the EB, the AB, staff, volunteers, or any members of its projects.
Differing viewpoints: CAM publishes articles with differing viewpoints in an effort to nurture vibrant debate and thoughtful critical analysis. Feel free to comment on the articles in the comment section and/or send your letters to the Editors, which we will publish in the Letters column.
Copyrighted Material: This web site may contain copyrighted material the use of which has not always been specifically authorized by the copyright owner. As a not-for-profit charitable organization incorporated in the State of New York, we are making such material available in an effort to advance the understanding of humanity’s problems and hopefully to help find solutions for those problems. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. You can read more about ‘fair use’ and US Copyright Law at the Legal Information Institute of Cornell Law School.
Republishing: CovertAction Magazine (CAM) grants permission to cross-post CAM articles on not-for-profit community internet sites as long as the source is acknowledged together with a hyperlink to the original CovertAction Magazine article. Also, kindly let us know at info@CovertActionMagazine.com. For publication of CAM articles in print or other forms including commercial internet sites, contact: info@CovertActionMagazine.com.
By using this site, you agree to these terms above.
About the Author

Valeriy Krylko is a freelance journalist, and translator of news articles in online media (English-Russian).
These articles are published in European and Russian-language media.
He is closely affiliated with independent outlets covering the Ukrainian-Russian conflict, and can be reached at: vkrylko098@gmail.com

