
[Because this series has been the result of a collaboration among three writers with extensive knowledge about 9/11, U.S. hegemony, and the commonly suppressed aspects of our system of governance, our authors decided to take a different approach with Part 3. Rather than present one consensus conclusion, they present here three separate concluding sections—one from each author. We hope this format takes full advantage of the unique perspectives that each have to offer.—Editors]
– Ben Howard –
In reflecting on 9/11 and the preceding terror attacks, it is clear that the security services’ long-entrenched practice of withholding and compartmentalizing information has had disastrous consequences. Contrary to the sentiments expressed in the press and by members of the 9/11 Commission and Joint Intelligence Inquiry, these disastrous consequences were far from accidental. Instead, as I believe we have demonstrated in Parts 1 and 2, this practice of withholding and compartmentalization has, at key moments, been employed for the purposes of allowing terrorist attacks against Americans and American interests.

These terrorist attacks are illegal but are essential for maintaining the present political economy. As demonstrated in Parts 1 and 2, they are often crucial to achieve the political and economic goals of the ruling class. The disastrous withholding of information by intelligence agencies and other covert groups is therefore necessary so these planned attacks are not foiled before they serve their intended purposes. Deep events, carried out with secrecy and subterfuge as they are, are often so submerged that even elements of the national security state cannot fully glean their breadth and scope.
It is no surprise, then, that the public has a limited understanding of these events. Much of this can be attributed to the unknown but certainly large amount of highly relevant information that has been concealed through dubious means, ranging from the improper classification of documents up to destruction of evidence and perjury. However, despite this suppression of information, many important stories and facts which belie establishment myths and narratives appear in prestigious newspapers or are reported by official government inquiries. That these stories and facts are not broadly known and incorporated into our collective understanding of our system is evidence of some other, more subtle, means of suppression.
Indeed, while many well-educated and well-read Americans may acknowledge that the official story of a deep event like, say, 9/11 is “something of a whitewash,”[1] bourgeois norms typically prevent these people from delving too deeply into that which is being whitewashed. These deep events point to the conclusion that the world we live in is often ruled by dark and occulted forces which escape accountability thanks to state secrecy, media manipulation, and the powerful psychological forces of repression, denial, and dissociation. But to acknowledge the implications of this conclusion for our nominal democracy is to situate oneself outside of acceptable discourse. It is clear, therefore, that to develop a proper understanding of the nature of the American politico-economic system, we must transcend this “acceptable discourse.” Our present understanding of America’s history and politics, manipulated as it is by ruling class interests, cannot serve us.
It is necessary, then, to develop a popular “common sense” counter-narrative which, through unflinching analysis of the role of class power and elite self-interest in our society, is able to capture and convey the true significance of these deep events. I am under no illusions that one article series, no matter how finely crafted or diligently researched, can change the course of history. That said, I am hopeful that it might contribute in a small way to the creation of a new and better understanding of history and politics we so desperately need. I remain optimistic that the great masses of people in this country and across the world, armed with more of the truth, will change the world for the better.
– Aaron Good –
Cutting Through the Parapolitical Fog of 9/11
The evidence and analysis in Parts 1 and 2 provide reasonable justification for seriously exploring the possibility that 9/11 was in some way facilitated by obscure elements of the state. Sadly, the vocabulary for investigating such an operation is lacking in the popular discourse. “False flag” refers to an old naval ploy wherein a vessel flies a different flag and attacks a target in order to inculpate the chosen party.
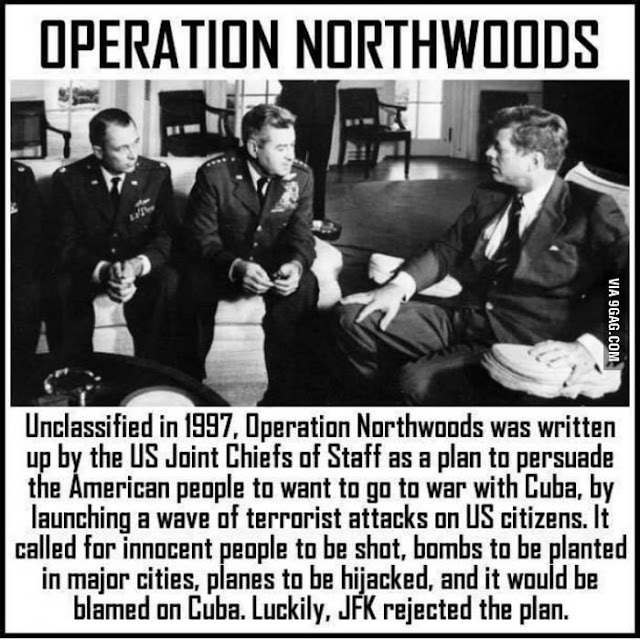
A version of such an operation was infamously carried out by the Japanese in the Second Sino-Japanese War to provide a pretext for further aggression against Manchuria. Similarly, Operation Northwoods included plans to have Cuban exiles dress up as Cuban communists and carry out attacks to justify a U.S. attack on Cuba.
Whatever the origins and ultimate controlling power of al-Qaeda was or is, its foot soldiers would appear to be, by and large, fanatical Islamists who are not conscious U.S. agents. Therefore, “false flag” is an imprecise description.
An “inside job” is something like, say, a bank robbery in which a bank employee serves as an “inside man” who plays a role in the robbing of the bank where he works. The “inside man” may have confederates who may or may not work at said bank. We accept that there are Islamist al-Qaeda terrorists who want to attack American, British, and Israeli targets (etc.).
That said, it is very improbable that there were high U.S. government officials who were secretly al-Qaeda agents bent on waging jihad. To put it mildly, al-Qaeda’s worldview and mission are not likely to appeal to persons with the wherewithal and inclination to advance in the U.S. national security bureaucracies. So again, “inside job” is not a term that can adequately capture the 9/11 terror spectacle.
This is not to say that 9/11 could not have had any aspects for which the terms “inside job” or “false flag” might be applicable. However, such categorizations are oversimplified and insufficient.
In order to assess the possibility that the 9/11 terror spectacle was in some way facilitated by elements of the state, it is important to have a framework of historiographical/social science theory. Since two of our co-authors, Peter Dale Scott and I, have previously produced scholarship in this vein, I offer a review of sorts.
In the 1970s, Scott began to explore the various national security state intrigues related to things like Vietnam, Laos, the heroin traffic, the assassinations of the 1960s, and Watergate. He coined the term parapolitics to describe “a system or practice of politics in which accountability is consciously diminished.”[2]

Eventually, Scott expanded these ideas into his study of deep politics: “all those political practices and arrangements, deliberate or not, that are usually repressed in public discourse rather than acknowledged.”
For a number of years, Scott maintained in his writings that the democratic state in the U.S. coexists with a deep political system “which habitually resorts to decision-making and enforcement procedures outside as well as inside those publicly sanctioned by law and society.”[3]
Key elements of the deep political system include the interplay between the overworld of private wealth and the underworld of organized crime. “Corruption,” rather than being a collection of anomalous phenomena, was a systemic feature resulting from practices and arrangements among criminal organizations, the wealthy, and public officials—including law enforcement.
Scott’s analysis differs from conventional liberal understandings in that he does not describe a healthy system that experiences corruption from time to time when officials make poor life choices. Rather, the underworld and overworld were, and are, always interacting and coexisting in different ways—along with the political system.
After World War II, the U.S. created a globally oriented, clandestine intelligence service. Throughout the Cold War and up to the present, CIA covert operations have served to further empower and enshrine deep political elements in the U.S. and abroad as American power was projected across the globe.

Eventually, Scott became the first North American scholar to use the term deep state in reference to the U.S. In 2015, he described the deep state as “a milieu both inside and outside government with the power to steer the history of the public state and sometimes redirect it.” Though the deep state should not be thought as a formal organization, Scott acknowledges that there are “extragovernmental structural components in the deep state system.”[4]
This deep state concept was derived from dual state theorists who, looking at the example of Nazi Germany, grappled with the notion of a dictatorial prerogative state that coexisted with the normative (or public) state—i.e., the government that we learn about in civics classes and such.[5]
In 2015, I built on the work of Scott and others by describing a tripartite state “comprised of the democratic state, the security state, and the deep state.”[6] In the tripartite state system, the deep state is key, as it largely subordinates or coopts the public state as well as the security state. In American Exception (my doctoral dissertation), I defined the deep state as:
…the various institutions that collectively exercise undemocratic power over state and society. Pluralistic to varying degrees, the deep state is an outgrowth of the overworld of private wealth. It includes most notably the institutions that advance overworld interests through the nexuses connecting the overworld, the underworld, and the national security organizations that mediate between them.[7]
It is my contention that U.S. democracy and the nature of the American state have been greatly impacted and even transformed by supralegal interventions into politics. Such events, which Scott terms deep events or structural deep events, point to an exceptionalist realm of state action.
The German theorist and Nazi, Carl Schmitt, famously wrote that “Sovereign is he who decides on the exception.”[8] Essentially, this means that the sovereign authority of the state ultimately rests with the party who decides when an exception to the rule of law is to be made in an emergency. According to Schmitt, the “state of exception” cannot be “codified in the existing legal order. [It is] a case of extreme peril, a danger to the existence of the state.” Notably, he adds that the state of exception “cannot be circumscribed factually and made to conform to a preformed law.”[9]

Again looking at Carl Schmitt—and as referenced earlier—another of my central arguments is that the U.S. has come to be characterized by exceptionism, an unending “state of exception” that is institutionalized if not acknowledged. Initially, these exceptionalist measures were ostensibly adopted in response to communism. Tellingly, they were never abandoned after the Cold War.[10]
The lawlessness of the American state should be well-known to CovertAction Magazine readers—CIA overthrows, assassinations, COINTELPRO, illegal invasions, collaborations with organized crime, etc., etc. Furthermore, it is a virtual certainty that what is known is but the tip of a larger iceberg.
Deep Events and the “Doomsday Project” in Light of Exceptionism
The “Doomsday Project” or Continuity of Government (COG) networks are significant elements that may hold keys to understanding important aspects of America’s deep history. Peter Dale Scott wrote extensively about COG in The Road to 9/11 and in The American Deep State. Some of what follows here is addressed later in greater detail within Peter’s concluding sections. Since Peter and I both believe that this material is of great significance, I think the repetition is useful or at least acceptable.
To summarize, the U.S. government created an organizational network whose purpose was to maintain a command structure even in the event of a catastrophe that might otherwise decapitate the government. Initially, the plans were formulated to deal with possibilities arising from a potential Soviet nuclear strike.
Though shrouded in secrecy to this day, COG planning was expanded over decades to include operations arising from a terrorist attack and/or from domestic unrest which would be deemed to warrant the massive detention of dissidents and the imposition of large-scale censorship.[11]
Scott has identified COG threads running through those episodes which he classifies as structural deep events (SDEs)—pivotal historical episodes that “are large enough to affect the whole fabric of society, with consequences that enlarge covert government.” These events “are subsequently covered up by systematic falsifications in media and internal government records.”[12]
Scott characterizes the JFK assassination, Watergate, Iran-Contra, and 9/11 as structural deep events. Based on Scott’s research into its obscure but recurrent role in these events, the scope of COG may be even broader and more obscured by state secrecy than we can surmise from the available record.

James McCord was a key figure that Scott identified as a recurrent actor in COG operations.[13]

In this context, it is noteworthy that McCord was identified as the CIA Office of Security officer who was charged with handling the fallout of the 1953 death of MKULTRA scientist Frank Olson. Olson’s demise was the result of a high-speed collision with the pavement following his tenth-floor hotel room defenestration.[14]
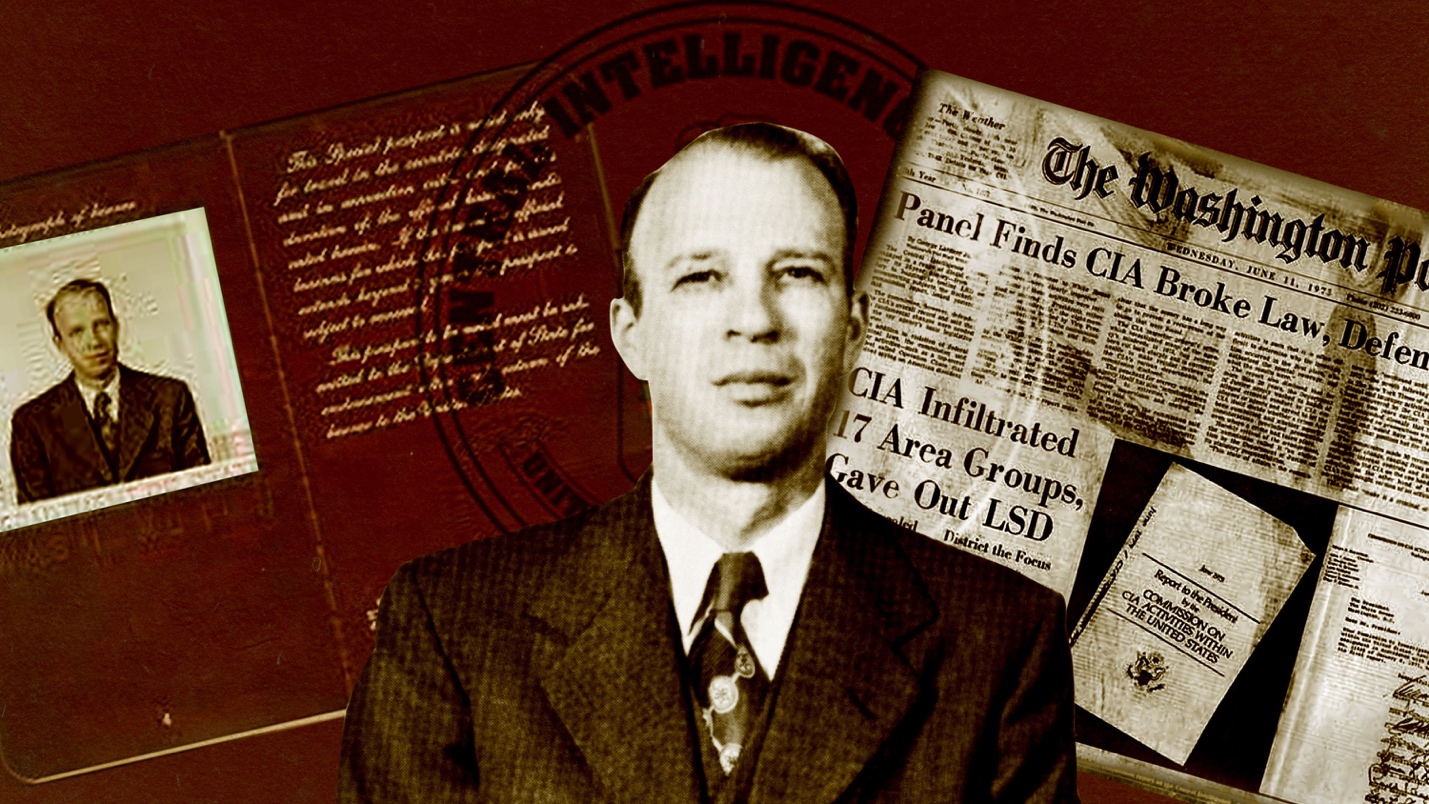
Though the government has never issued an acceptable official account of Olson’s death, Seymour Hersh eventually learned from a highly placed source that Olson had been ruled a security risk and subsequently dispatched. As described by The New York Review of Books, this national security mechanism authorized “the execution of internal dissidents by the CIA’s [James McCord-headed] ‘Office of Security.’”[15]
Such revelations would seem to confirm E. Howard Hunt’s 1975 assertion that the agency made use of a team of assassins charged with neutralizing security threats such as individuals deemed double agents or even employees of the CIA.[16]

As I wrote in American Exception, these matters raise a number of important questions and grave possibilities:
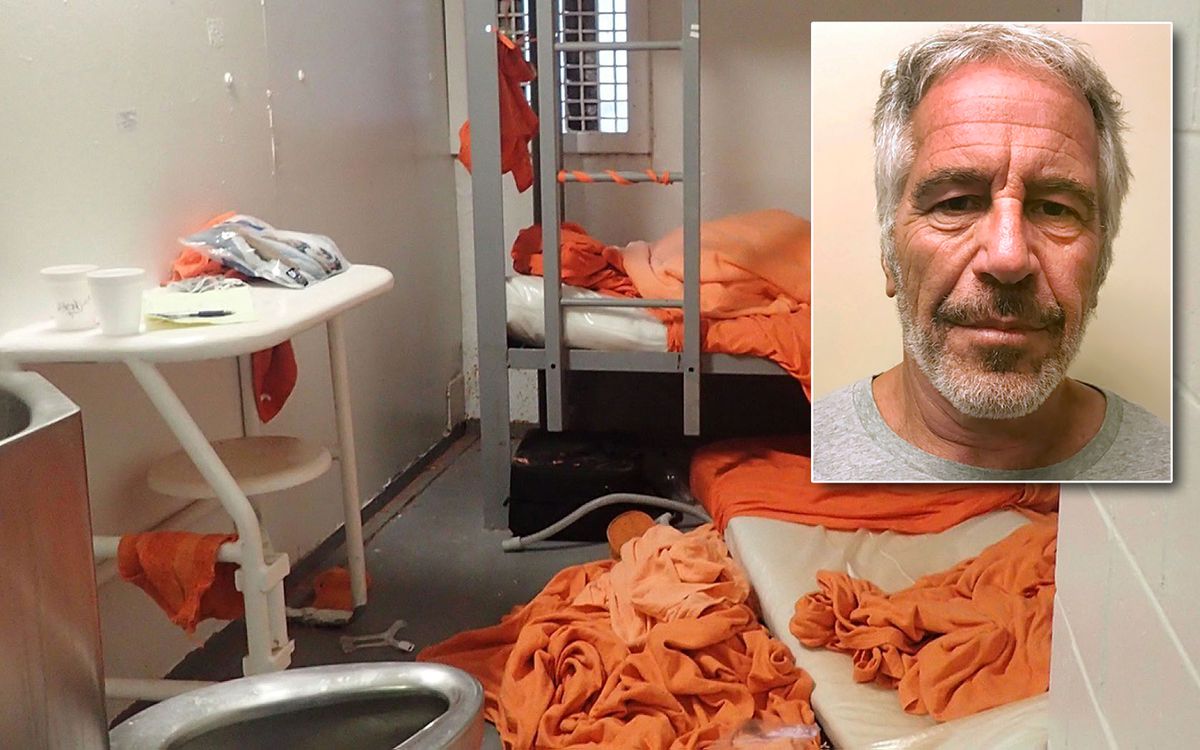
Do Doomsday/COG provisions allow for supralegal covert actions to be carried out domestically in the name of national security? Do such provisions deem U.S. hegemony, in some respect, to be a core element of national security—an element whose perpetuation must be safeguarded? Would exposure of the most egregious state crimes be considered the kind of threat to national security that would necessitate exceptionist measures? This is another way of asking whether American exceptionism extends to authorizing actions undertaken to maintain the concealment of exceptionism from U.S. and global publics. Could such secret provisions explain McCord’s role (as well as the CIA’s) in Frank Olson’s apparent summary execution? Could such provisions also explain in part the historically unique manner in which the press and the national security bureaucracy coalesced against Nixon? Might such policies help to illuminate other strange events such as the suspicious recent deaths of Michael Hastings or Jeffrey Epstein? Of course such matters are academic in the vernacular sense without the dramatic weakening of U.S. state secrecy.[17]
All of this is to suggest that there may be state actors with the ability to take supralegal executive action with covert sanction from the state. Such mechanisms may be intertwined with Doomsday/COG networks, thus they may benefit from the overriding authority and utmost secrecy therein.
Doomsday/COG: A Key to the Mystery of 9/11?
Regarding 9/11, this line of inquiry has some relevance in light of a number of factors. First, there is the fact that Dick Cheney and Donald Rumsfeld were both members of an ultra-secret committee drafting COG provisions in the 1980s under Reagan. Cheney at the time was a congressman, and Rumsfeld was a pharmaceutical executive.[18]

Although it was reported in The New York Times that “the Doomsday Project” had been shut down in the post-Soviet Clinton years, planning and exercises continued in the 1990s with terrorism replacing nuclear war as the basis. Cheney and Rumsfeld were again part of these COG operations, working as part of a collection of right-wing hawks that one Pentagon official described as “a secret government in waiting.”[19]
There is also the still-secret use of COG elements on 9/11 following the activation of COG measures on the day of the attacks. In The Road to 9/11, Peter Dale Scott extensively detailed what is known about the still largely obscured role of COG on 9/11, especially as regards the strange actions of Dick Cheney.[20]
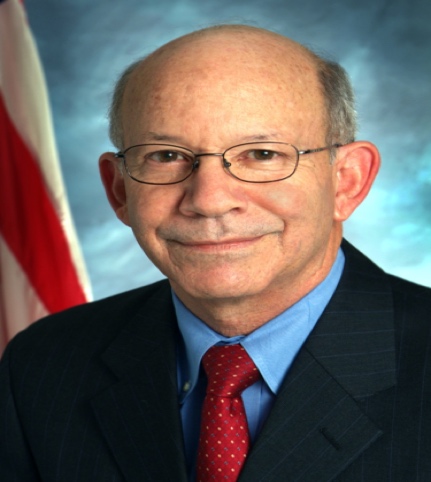
Additionally, in the aftermath of 9/11 and up to the present, unspecified emergency provisions have been reauthorized by a U.S. Congress that is not allowed to know the full details of what is being reauthorized. When a member of the Homeland Security Committee, Congressman Peter DeFazio (D-Ore.), requested to see Bush administration annexes to COG emergency provisions, he was twice denied.[21]
Given the foregoing, one cannot rule out the possibility that some sort of overriding prerogative powers were exercised through COG/Doomsday channels in such a way as to influence events before, during, and/or following 9/11.
Perhaps such could help explain those episodes, detailed in Part 2 of this series, in which various legitimate state actors were stymied just as they were close to exposing or interfering with the unfolding 9/11 conspiracy. If indeed COG/Doomsday networks are vested with the responsibility of safeguarding the state from existential threats up to and including nuclear war, the requisite prerogatives could well mean that such entities are ultimately sovereign in the Schmittian sense and thus not subject to legal circumscription or public oversight.
A logical corollary is that such entities would necessarily have to determine when a situation does or does not represent a threat to core national security imperatives or interests. Democratically elected officials like Congress or the President may or may not have had decisive input in defining the scope and authority of such entities. Furthermore, these opaque networks may have considerable independence in defining those core national security imperatives or interests in the first place.
Beginning with The War and Peace Studies Project in World War II, various U.S. elites in and out of government have advocated essentially for U.S. hegemony over the global capitalist system and/or the unrestrained use of state power to defeat threats to U.S. hegemony.[22] Most notably, these included the threats ostensibly posed by the “global communist conspiracy.” In practice, however, we see the repeated pattern of the U.S. often acting against non-communist, even democratic governments—especially those countries guilty of “resource nationalism,” i.e., countries guilty of attempting to utilize their respective resource wealth in ways that benefit their own citizenry.[23]
If deep political elements do prevail within the COG/Doomsday networks vested with overriding prerogative powers and control of state secrecy, such a constellation of powers could have been utilized to facilitate the events of September 11, 2001, and/or to influence the events’ impacts.
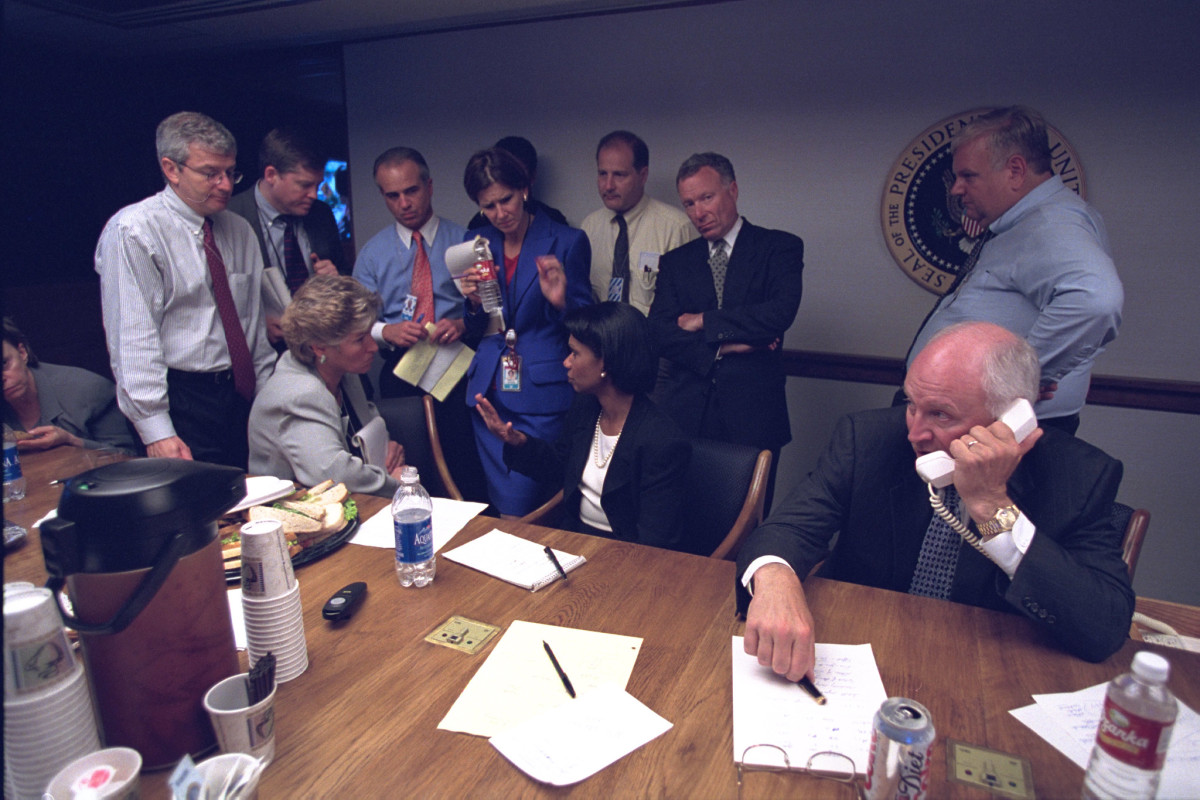
One grim possibility could be that COG/Doomsday provisions were established by Cheney and Rumsfeld (or like-minded actors) in such a way as to allow COG-affiliated networks to carry out covert operations without presidential authorization. In such a scenario, people like CIA Director George Tenet and CIA officer Richard Blee and others could have functioned as fail-safe actors, holding key positions that granted them controlling authority over the most sensitive elements related to al-Qaeda.

George Tenet [Source: wikipedia.org] 
Richard Blee in his high school yearbook. [Source: historycommons.org]
Meanwhile, al-Qaeda could be funded and managed covertly by highly secretive elements within or above the intelligence services of other countries, Pakistan and Saudi Arabia in this case. Figures like Tenet and Blee would not have needed to know precisely why they were protecting certain figures or operations from exposure. However, given that Blee’s protection coincided with his famous warning about impending “spectacular” attacks, it is harder to conceive of him as totally unwitting.
Another similar COG/Doomsday explanation could explain the U.S. response to 9/11 and the subsequent cover-ups of crucial aspects of the event. In such a scenario, networks affiliated with the neoconservatives could have set the stage for 9/11 without any formal sanction from overriding COG entities.
Then on the day of the attacks, provisions could have been enacted which granted the administration overriding control of COG/Doomsday networks and their attendant prerogative powers. Such may include the secret authority to manage information and conduct governance in accordance with what the administration deems necessary for security in the face of an existential threat.
The very activation of COG measures on September 11, 2001, indicates that the attacks were deemed to be an emergency of that magnitude. If complicit administration figures subsequently activated COG/Doomsday measures during the attacks, such may have allowed them to exercise various prerogative powers—ostensibly to respond to the crisis, but perhaps in practice to use the full emergency powers of the state to prevent exposure of key incriminating acts and actors.
Given state secrecy, the hashing out of such possibilities cannot rise above the status of elaborated hypothesis. That said, when one accepts the well-documented historical facts of widespread state lawlessness and high levels of state secrecy, there is no basis for the a priori rejection of hypotheses which raise the possibility of clandestine state complicity in violent events of great politico-economic significance such as 9/11.
Reflexive denunciations of explanations which posit covert state criminality likely reflect a number of social forces. Such would include, perhaps: (1) the hegemony of deep political forces over the “common sense” that prevails at liberal institutions like the media and academia; (2) the common human tendency of suppressing traumatic experiences; (3) the similar but less intense human responses which reflexively seek to minimize cognitive dissonance and maintain individuals’ core worldviews; and (4) the unknown extent to which deep political forces have actively manipulated culture to obscure top-down governance of a nominally democratic political order.
Collectively, these and other dynamics have short-circuited the ability of a democratic polity to hold the ruling elite accountable. The general stupefaction of mainstream discourse on these matters has accelerated since 9/11. Prevailing conventional taboos about “conspiracy theories” are nonsensical and yet routinely invoked. We are told that “conspiracy theories” about 9/11 are unacceptable even as the state’s theory of 9/11 is that it was the result of a conspiracy.

Symptomatic of this enforced myopia was the mainstream response to the grand Russiagate conspiracy theory, a spectacle which to date has failed to produce any convictions for conspiracy or treason. In this case, the critics of the Russiagate conspiracy theory were actually themselves denounced as “conspiracy theorists.” Thus, among other things, Russiagate provided further support for the claim that the mainstream usage of the term “conspiracy theory” is simply a way to stigmatize and dismiss critics of official pronouncements.

U.S. elites’ Orwellian subversion of democratic sense-making through such means is not incomprehensible. Americans have lived through vast amounts of official deception for which the responsible parties have not been held accountable. Since few Americans at this point would be persuaded by loud assertions of the state’s integrity and rectitude, there is a logic to the use of weaponized speech to discredit, a priori, any explanations that raise the specter of high criminality.
I am not in a position to state authoritatively whether or not exceptionalist Doomsday/COG elements played a role in bringing about the terror spectacle of September 11, 2001. Regardless, American democracy could not but benefit from an American glasnost—a great opening up of that which the state has concealed from the U.S. public since the country began to pursue global hegemony after World War II.
Presently, the U.S. has just experienced a demoralizing defeat in America’s longest war, the war in Afghanistan for which 9/11 provided the initial pretext. Short of launching an apocalyptic nuclear war, there would seem to be no way to reverse the decline of U.S. global dominance. The U.S. is going the way of all empires.

Though the 9/11 wars should be recognized as reckless gambits to prevent this outcome, they likely hastened it. Now in 2021, having failed to use America’s considerable power to confront looming crises of climate change and staggering inequality, perhaps it is time for U.S. elites to abandon the covert empire—the empire that denies its imperial status by creating myths and cover stories to obscure its strategies and tactics.[24]
For some observers, Obama seemed to offer a chance to wind down the empire after the disastrous Bush years. Instead, he largely consolidated and extended the hegemony of the imperial-minded deep state over U.S. society. Astoundingly, the U.S. under Obama managed to revive the pre-9/11 practice of using al-Qaeda as U.S. proxies in Libya and Syria—a fact whose suppression stands as a monument to the efficacy of the propaganda model that prevails in the U.S.

But events beyond the control of U.S. elites are coming to the fore. At this late hour, international cooperation and justice-minded reforms offer the best chance to avert catastrophic outcomes that will not leave the powerful unscathed. U.S. elites risk becoming victims of their own totalizing governance: In assessing present day American society, it is clear that the Enlightenment—the presumptuous control of humanity’s fate by way of reason—has been diverted from delivering on its promises.
If at present we are dominated by top-down, anti-Enlightenment forces, perhaps the truth can yet set us free. Necessary first steps would include ending the post-9/11 states of emergency—perhaps in conjunction with the revelation of crucial state secrets which have been hidden for antidemocratic, imperialist reasons. In such a way, we might initiate an era of truth and reconciliation in the U.S. In turn, such a cataclysm might serve as a catalyst for the international cooperation that is necessary if humanity is to respond to our mounting civilizational crises.
– Peter Dale Scott –
In The American Deep State I wrote about America’s structural deep events (SDEs), in which “from time to time dark forces intervene to redirect American policies, such as … 9/11, which launched the global terror war.”[25] I also suggested that there were common features linking America’s structural deep events, above all their involvement with the so-called “shadow government” or “Doomsday Network” set up in the 1950s to provide “continuity of government” (COG) in the event of a devastating nuclear attack.
Another feature of these structural deep events is that, while they are attributed to very marginal elements—such as a disgruntled ex-Marine, or 19 angry Arabs—sooner or later key figures in power, in the course of a cover-up, are caught lying about what actually happened.
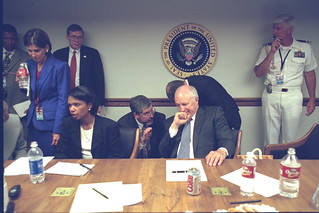
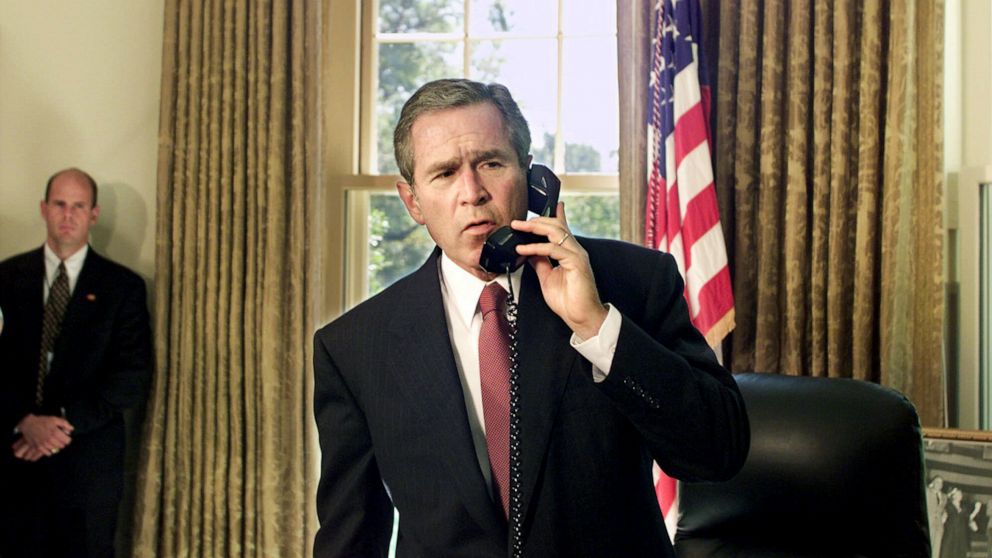
In the case of 9/11, Vice President Cheney provided two incompatible accounts of when he arrived at the underground Presidential Emergency Operations Center (PEOC), where crucial decisions were made in the half-hour between 9:30 and 10:00 a.m., including the decision to implement COG. Cheney himself told NBC five days later that he arrived to make decisions at the PEOC shortly before the Pentagon was attacked (at 9:37 a.m.).

But in December, after disturbing allegations about Cheney’s activities in the PEOC were made by eyewitness Norman Mineta, Cheney gave a later arrival time to Evan Thomas of Newsweek: “Shortly before 10 a.m., the Cheneys were led into the PEOC conference room. [T]hey looked up at the TV screens. It was 9:58 a.m.”[26]
How did the 9/11 Commission resolve this conflict? By accepting the second time as if unquestioned, and simply ignoring the earlier, much more corroborated story. And how did it deal with Norman Mineta’s very disturbing testimony? By simply ignoring it as well.[27]

I can now be slightly more specific about those dark forces, in two respects. To begin with, in all of America’s SDEs to date, an initial, more marginal plot for a deep event was then piggy-backed on and exploited, for a different goal by a more institutional plot.
In the case of 9/11, there was indeed a plot of al-Qaeda Arabs to capture U.S. passenger planes, perhaps to fly them suicidally, but also imprecisely, into the areas of New York and Washington.[28] This plot was detected and exploited by an American dark force, using the Arabs as designated culprits in a piggy-backed plot with a much more ambitious target: to fly planes into the Twin Towers and the Pentagon.[29]
I can also be more specific than before about this second dark force. In earlier books I have written about how, in each of America’s SDEs, a major role has been played by the COG apparatus, also known as the “Doomsday Network”—i.e., the communications network developed over decades at considerable expense to provide the skeleton for governing authority after a decapitating nuclear attack. More specifically, America’s SDEs have involved those individuals charged with secret COG planning for America’s secret Doomsday Network, as well as the COG/Doomsday Network itself.[30]
It is now quite clear to me, as it was not before but should have been, that those planning for the Doomsday Network were also in charge of operating it, if it was ever used. I will argue in this essay that two men known to have planned the Doomsday Network in the 1980s and 1990s were also part of the dark force which caused 9/11 to happen, and then officially implemented the COG plan which had already been used on that day.
The two men were Dick Cheney and Donald Rumsfeld, both part of a secret committee appointed by Reagan to plan for, in effect, a post-constitutional replacement of constitutional authority. Notably, neither man was a part of the U.S. Government while serving in this COG-planning capacity. Throughout the ’80s and ’90s, Rumsfeld was CEO of G.D. Searle, a Big Pharma corporation. Cheney, initially a congressman, became CEO in the ’90s of Halliburton, the giant oilfield service corporation.[31]

Evidence that COG planners were also potential operators was discovered by accident, in May of 1961, by Kennedy’s White House assistant Fred Dutton. In that month he wrote a memo to his superiors of a startling discovery: “the existence of classified letters from President Eisenhower to ten private citizens throughout the country giving them authority over various parts of the economy and total society in the event of a declaration of a national emergency…”[32]

This was in response to the vulnerability revealed by the USSR’s successful launch of Sputnik, after which Ike’s cabinet commissioned, in the event of a nuclear attack, new “executive agencies” to provide “the means by which a fragmented federal government could begin to exercise authority over a devastated nation.” [33]
Why did Eisenhower add private corporate managers to U.S. armed forces and law enforcement as a replacement for a constitutionally elected government? He may well have been concerned about anti-democratic groups then spreading within the U.S. armed forces and police, especially after the Supreme Court decision in 1954 to enforce school desegregation nationwide. Some of these right-wing cliques had actually established contact with post-war fascist residues in Europe.

But it did not take long for Eisenhower’s emergency alternative (soon to become known to those in the know as the “Doomsday Project”) to become anti-democratic as well. A dangerous feature of the Doomsday Project was that in it there was no real separation of powers: Those who were planning for post-attack structures, like Frank Stanton, were also charged with implementing them. From the standpoint of preserving American democracy, this would prove to be a fatal weakness.

Under both Republicans and Democrats in the 1970s—a decade of assassinations, massive anti-war protests, and black militancy—the powers of the Doomsday Project continued, without interruption, to grow. For example, both Nixon and Ford expanded the development of plans to establish government control in the event of any (as opposed to post-nuclear) “national emergency.”[34]
Financial expert Howard J. Ruff commented that, since the enactment of Executive Order 11490 in 1969, “The only thing standing between us and a dictatorship is the good character of the President and the lack of a crisis severe enough that the public would stand still for it.”[35]


In that troubled era, among the many establishment figures warning that America was becoming ungovernable was Harvard Professor Samuel Huntington, who co-wrote (for David Rockefeller’s Trilateral Commission, of which he was a member) a book arguing that America’s problems stemmed “from an excess of democracy.”[36]
Huntington then joined the Carter administration as a consultant to National Security Adviser (and former Trilateral Commission Director) Zbigniew Brzezinski.[37] Together the two were responsible for the creation in 1979 of the Federal Emergency Management Agency (FEMA). In addition to its high-profile public functions, FEMA inherited the secret function of sustaining and enhancing the Doomsday Project (or COG).[38]

Under Reagan, FEMA’s public role of disaster relief
…was neglected and starved of resources, while the [secret function] flourished. FEMA set up a “Civil Security Division” with a training center for over 1,000 civilian police to handle riots and political disturbances (not disaster relief). A file was gathered on U.S. left-wing activists, and internment camps were planned. One national training exercise [REX 84] envisioned incarcerating 100,000 “national security threats.” [39]
In particular,
…a small division of FEMA, the National Preparedness Division (NPD), was charged with developing a classified computer and telecommunications network to insure [sic] the continuity of the government in the event of a nuclear attack.[40]
This network, known in house as the Doomsday Network, mushroomed; at a cost of billions, it became a global secret communications network from which those administering FEMA’s legitimate functions were excluded.
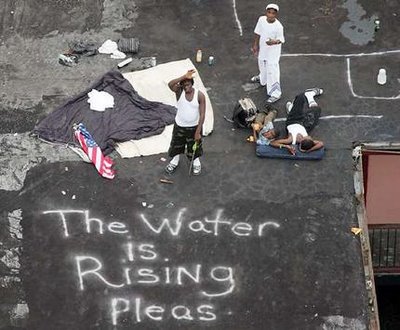
Thus, for example, in 2005, when FEMA’s civilian administrators were struggling to restore communications after Hurricane Katrina, the resources of the Doomsday Network, which would have been of vital use, were unavailable (and probably unknown) to them in their lawful activity.[41]
But when Oliver North was engaged in unlawful arms sales to Iran, the Doomsday Network (known then as Flashboard) was available to him, as a necessary way to avoid bureaucratic review.[42]
North’s manic overreach with FEMA’s secret powers aroused widespread resentment inside Washington, and soon led to leaks. In July 1987 Alfonso Chardy reported in the Miami Herald that North’s and FEMA’s plans envisaged
…suspension of the Constitution, turning control of the government over to the Federal Emergency Management Agency, emergency appointment of military commanders to run state and local governments and declaration of martial law during a national crisis.[43]
That Chardy’s claims were not unfounded was confirmed during the Iran-Contra hearings, when Congressman Jack Brooks (D-Tex.) asked North if he was involved in “plans for continuity of government … a contingency plan … that would suspend the American constitution.” The Democratic Committee Chairman, saying that “that question touches upon a highly sensitive and classified area,” directed North not to answer. The New York Times transcribed the hearing. But did not consider that the possible suspension of the U.S. Constitution was worthy of a news story.[44]

9/11, COG, and the 9/11 Commission Report
On 9/11, with Bush away from the capital, Cheney and Rumsfeld implemented the COG plan which they had been secretly planning for two decades. The 9/11 Commission Report confirms this fact, which had immense consequences.[45]
Under COG, according to The Washington Post, Bush
…dispatched a shadow government of about 100 senior civilian managers to live and work secretly outside Washington [to Site R, Raven Rock Mountain Complex]. Known internally as the COG, for “continuity of government,” the administration-in-waiting is an unannounced complement to the acknowledged absence of Vice President Cheney from Washington for much of the past five months.[46]
According to Professor Shirley Anne Warshaw,
Cheney jumped into action in his bunker beneath the East Wing to ensure continuity in government. He immediately began to create his shadow government by ordering one hundred mid-level executive officials to move to specially designated underground bunkers and stay there twenty-four hours a day. They would not be rotated out, he informed them, for ninety days, since there was evidence, he hinted, that the terrorist organization al-Qa’ida, which had masterminded the attack, had nuclear weapons.[47]
It would appear that this “shadow government” finalized such long-standing COG projects as
- warrantless surveillance, in part through the USA PATRIOT Act, whose controversial provisions were already being implemented by Cheney and others well before the Bill reached Congress on October 12.
- the militarization of domestic security under NORTHCOM, so that the Pentagon would be involved in the surveillance of U.S. citizens.
- Department of Homeland Security’s Project Endgame—a ten-year plan to expand detention camps at a cost of $400 million in fiscal year 2007 alone. This means of handling protest movements, which Rumsfeld and Cheney had rehearsed in REX 84, was an important corollary at the time to the decision, already reached, to again conduct a major war in Central Asia.
Congress, however, was not told that the U.S. was now under a continuity of government status until February 2002:
Senate Majority Leader Thomas A. Daschle (D-SD) said he had not been informed about the role, location or even the existence of the shadow government that the administration began to deploy the morning of the Sept. 11 hijackings. An aide to House Minority Leader Richard A. Gephardt (D-MO) said he similarly was unaware of the administration’s move.[48]

Tom Daschle [Source: cnn.com] 
Richard Gephardt [Source: gephardtgroup.com]
The radical alterations in previous decades of COG planning were now clear. Eisenhower’s project of a successor government was implemented by Cheney and Rumsfeld as a shadow government, one existing alongside the still-existing government, but at a higher level of secrecy to which America’s constitutional government and its citizens were denied access.[49] It was this anomaly that led me to suggest, in The Road to 9/11, that America was now being governed by a “deep state.”
Cheney on 9/11 used COG to sideline, not just Congress, but Attorney General John Ashcroft and other top leaders of the Bush administration. To accomplish his goals, according to Barton Gellman of The Washington Post,
[T]he vice president and his lawyer [David Addington] had to set the government’s legal direction.… By the afternoon of September 11, Addington had made contact with Timothy Flanigan, the deputy White House counsel. Flanigan’s boss, Alberto Gonzalez, was stranded in Norfolk.… Flanigan was in the [White House] Situation Room on September 11. When Addington reached him from the [underground] bunker, Flanigan patched in the Justice Department Command Center across town. There he found [sic] a young attorney named John C. Yoo [who] had taken leave from university life to join the [Justice Department’s] Office of Legal Counsel as a deputy.[50]
The important connection between these two lawyers, who shared extraordinarily similar views on the importance of prerogative powers, did not occur by accident. Yoo, the young deputy assistant attorney general for the Office of Legal Counsel, with only two months of government experience, was presiding at the Justice command center. Why such a junior official? Because Attorney General Ashcroft and those directly under him (his deputy Larry Thompson, and his assistant David Ayres) had all been ordered by the PEOC under COG rules to go elsewhere.[51]

John C. Yoo [Source: law.berkeley.edu] 
David Addington [Source: militarist-monitor.org] 
John Ashcroft [Source: wikipedia.org]
The Cheney-Addington-Yoo channel persisted, and was used for Yoo’s still-withheld 50-page memo on torture: “In an interview after leaving government, Yoo said Addington and Flanigan assisted in the preparation of that memo.” [52]
The Shadow Government after 2001
Shortly before leaving office. Reagan officially changed the purpose of COG planning: it was no longer for arrangements “after a nuclear war,” but for any “national security emergency.” This was defined in Executive Order 12656 of 1988 as “any occurrence, including natural disaster, military attack, technological emergency, or other emergency, that seriously degrades or seriously threatens the national security of the United States.”[53] It was under this expanded authority for COG that Cheney and Rumsfeld were able to implement it on 9/11. And we appear to be still officially in that state of emergency today.
Three days after 9/11, Bush used his authority under the National Emergencies Act to declare two White House Declarations of Emergency: Executive Order 13223 of September 14, 2001 (“Ordering the Ready Reserve of the Armed Forces to Active Duty”), and Executive Order 13224 of September 23, 2001 (“with respect to persons who commit, threaten to commit, or support terrorism).” Both of these EO titles point to foreign concerns; yet somehow, as we shall see in a moment, COG, which authorized Cheney’s shadow government, continues to exist beyond Congressional purview.
One of the post-Watergate restrictions in the Act is that a state of emergency will lapse after a year, unless the president renews it. Year after year, every September, presidents have renewed them: first, Bush, then Obama and Trump. On September 9 of this year, even as I was predicting Joe Biden would soon do the same, Biden renewed EO 13223.[54]
Another of the law’s restrictions specifies that:
Not later than six months after a national emergency is declared, and not later than the end of each six-month period thereafter that such emergency continues, each House of Congress shall meet to consider a vote on a joint resolution to determine whether that emergency shall be terminated (50 U.S.C. 1622, 2002).
The law does not permit Congress to review an emergency; it requires Congress to review it.
Yet in twenty years Congress has not once met in public session to discuss the State of Emergency declared by George W. Bush in response to 9/11, a State of Emergency that remains in effect today. Appeals to the Congress to meet its responsibilities to review COG have fallen on deaf ears, even during periods when the Congress has been dominated by Democrats.[55]
During this state of emergency, COG planning has continued to expand and Congress continues to be excluded from access to it. In 2007, Bush issued National Security Presidential Directive 51 with classified Annexes, setting out what FEMA later called “a new vision to ensure the continuity of our Government.”[56] Congressman Peter DeFazio of the Homeland Security Committee twice requested to see these Annexes. When his request was denied, DeFazio made a second request, in a letter signed by the Chair of his committee. The request was denied again.[57]
COG’s Partial Implementation on January 6, 2021, and What Was at Stake
Many readers may not know that on January 6th, the day of the insurrection at the Capitol, COG was implemented again.

The details are still in dispute, but on that day something like the following real-time report either happened, or almost happened:
Congressional leadership is being evacuated to D.C.’s Fort McNair, as lawmakers were forced to shelter in place and halt debate over the ratification of President-elect Joe Biden’s Electoral College win when a pro-Trump mob stormed the U.S. Capitol, U.S. law enforcement official said. The southwest Washington, D.C. Army base has been the backup location for Congress to meet in case of terrorist attack.[58]
Fort McNair is indeed a designated COG site for the relocation of Congress, and a relocation of Congress there was actually rehearsed back in 2004.[59]

It has been alleged, and also denied, that the reported evacuation to Fort McNair occurred. That it did occur would seem to be implied by a passage in a new book by Carol Leonnig and Philip Rucker, I Alone Can Fix It: Donald J. Trump’s Catastrophic Final Year:
At Fort McNair, meanwhile, about 150 National Guard members secured the entrances to the base, which was being treated as a continuity of government site since the Congressional leaders were there. They were getting the extra protection typically provided when the country was under attack.[60]
One person who realized the political consequences of this evacuation was Mike Pence, who by all accounts refused to comply with it. According to the account by Leonnig and Rucker, again disputed:
At 2:26, after a team of agents scouted a safe path to ensure the Pences would not encounter trouble, [Secret Service agent] Giebels and the rest of Pence’s detail guided them down a staircase to a secured subterranean area that rioters couldn’t reach, where the vice president’s armored limousine awaited. Giebels asked Pence to get in one of the vehicles. “We can hold here,” he said. “I’m not getting in the car, Tim,” Pence told him. “I trust you, Tim, but you’re not driving the car. If I get in that vehicle, you guys are taking off. I’m not getting in the car.” … Around this time, [Pence’s national security adviser, ret. Lt. Gen. Keith] Kellogg, ran into Tony Ornato in the West Wing. Ornato, who oversaw Secret Service movements, told him Pence’s detail was planning to take Pence to Joint Base Andrews. “You can’t do that, Tony,” Kellogg said. “Leave him where he’s at. He’s got a job to do. I know you guys too well. You’ll fly him to Alaska if you have a chance. Don’t do it.”[61]
Pence, by this account, refused to be disempowered on a pretext of COG, the way that Ashcroft had been disempowered back on 9/11.

Anthony Ornato was a Trump loyalist whom Trump, after trying unsuccessfully to install him as head of the Secret Service, had brought into the White House as Deputy Chief of Staff for Operations. In this capacity,
Ornato was among the coordinators of the June photo op for which Trump marched through Washington D.C.’s Lafayette Square to stand with a Bible – after peaceful protesters were forced from the area by troops on federal order, sparking uproar in political circles as well as among the public. Ornato also assisted in the planning of many Trump campaign rallies.[62]

At first glance, the astonishing slowness of the National Guard’s response to the Capitol violence might seem attributable to pro-Trump elements in the Pentagon. One man named was General Charles Flynn, brother of Trump’s first national security adviser Michael Flynn, who had “reportedly advocated declaring martial law as part of an effort to overturn the election.”[63]

But in the long run the delay in summoning the Guard may have done more to weaken than to strengthen Trump’s political chances. This was the case with the delay of arrests in the October 2020 plot to kidnap Michigan Governor Gretchen Whitmer, seen (according to The New York Times) “as a precursor to the violence unleashed at the U.S. Capitol on Jan. 6.”[64]
The FBI had been aware of the kidnap plot from its outset; the plotters included three FBI informants, including one “who’d advised them on where to put the explosives — and offered to get them as much as the task would require.”[65] Yet the FBI, as always, delayed arrests until enough indictable actions had been committed to ensure convictions in court.

Something similar appears to have happened on January 6. Here too the FBI had informants among those arrested at the Capitol, including one, Thomas Caldwell, who was allegedly a leader of the far-right Oath Keepers militia group accused of being the principal organizer of the attack.[66]

And here too the delay in response allowed multiple crimes to be committed, and subsequent arrests to be made. By August 30, 639 people had been charged in the Capitol insurrection.[67] Among them are several members of at least four of the right-wing militia groups that are now a clear domestic threat to the security of this country.[68] Some of those arrested have already agreed to turn state’s evidence, and testify for the prosecution.
On January 6, according to Leonnig and Rucker, Acting Defense Secretary Christopher Miller, Trump’s post-election replacement for Mark Esper, was pushing for a vigorous law enforcement response by 2:45 p.m. They attribute the delay in the arrival of Guard units from Maryland and Virginia to Army Secretary Ryan McCarthy, who “hadn’t gotten around to” authorizing their call up “until more than two and a half hours after the Capitol was breached.”[69] It may be relevant that, among the leaders in Trump’s Pentagon, McCarthy had been singled out by Defense News in December as a long-time defense official who would probably be kept on by Biden.[70]

In Conclusion …
It is far too early to state with confidence what really happened on January 6. But I feel confident in calling it a Structural Deep Event, one in which COG was involved, and about which we can expect lies in high places.
As I said at the outset, in all of America’s SDEs to date, an initial, more marginal plot for a deep event was then piggy-backed on and exploited, for a different goal, by a more institutional plot.
It would appear that, on January 6, insurrectionary militias like the Oath Keepers and Proud Boys plotted to use violence to forestall the confirmation of Biden as President. This plot was itself blocked (in other cases, one might have said, “trumped”) by a more institutional plan to use this very violence against the insurrectionists.

Time may someday confirm if members of the Secret Service used COG powers to augment the first plot, and if Ryan McCarthy delayed the arrival of the National Guard as part of the institutional response.
Or, if previous SDEs like the JFK assassination and 9/11 are a precedent, we may still be debating these issues decades from now.
Here is a more confident prediction. As I wrote in Deep Politics, the Warren Commission Report combined a finding that a disgruntled lone assassin killed John Kennedy with non sequitur recommendations that the Secret Service, together with the FBI and CIA, should increase and coordinate more closely the surveillance of organized groups.[71]
In like fashion, the 9/11 Commission Report, after confirming that COG was implemented on 9/11 (Report, 326, cf. 38), and also that “We did not investigate this topic” (Report, 555n9),[72] concluded with a recommendation that planning for “continuity of operations” should be increased (Report, 398).[73]
Relying on these precedents and absent a major political change, I predict that the House select committee investigating January 6 will recommend that the surveillance of Americans be increased, perhaps with greater NSA/CIA/FBI coordination.
But this would be exactly wrong.

This country is not suffering from a deficit of secret surveillance powers. It is suffering from a surfeit of secret powers, most of them never constitutionally authorized—powers that successively contribute to more and more deep events that are then used to justify their own further proliferation.
Just as foolish U.S. operations in Central Asia led to the formation of, first, al-Qaeda and, then, ISIS, so successive molestations of this country by its shadow government have led to the rise of outlandish and malevolent right-wing militias.

Militia group in Michigan. [Source: metrotimes.com] 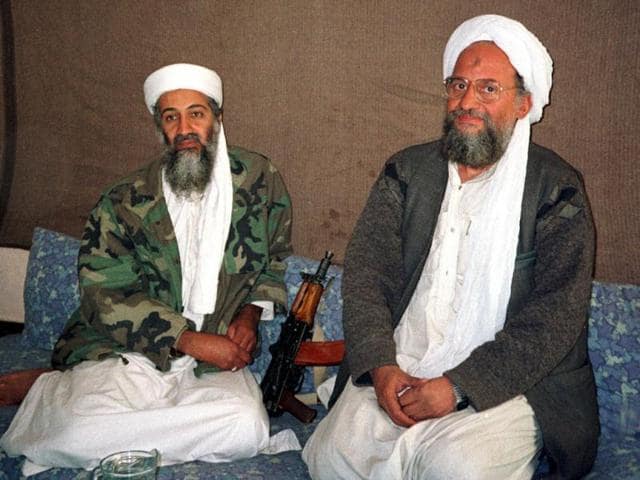
Osama bin Laden and Ayman Al Zawahiri of al-Qaeda. Both groups grew in response to misguided U.S. government policies.[Source: hindustantimes.com]
This country must move in the opposite direction. I can think of no better first step than to end the State of Emergency proclaimed in 2001, as a first step in dismantling the apparatus of fear and domination that has so distorted this country.
In my books I have called upon Congress to do this. But Congress will not take this action until the American people, aware at last of what has been going on, force them to do so.

-
Chris Hayes, “9/11: The Roots of Paranoia,” The Nation, December 25, 2006, https://www.thenation.com/article/politics/911-roots-paranoia/. ↑
-
Peter Dale Scott, The War Conspiracy (New York: Bobbs Merrill, 1972), 171. ↑
-
Peter Dale Scott, Deep Politics and the Death of JFK (Berkeley, CA: University of California Press, 1993), xi-xii. ↑
-
Peter Dale Scott, The American Deep State: Wall Street, Big Oil, and the Attack on U.S. Democracy (New York: Rowman & Littlefield, 2015), 199-200: n. 63. ↑
-
Ernst Fraenkel, The Dual State: A Contribution to the Study of Dictatorship (New York: Oxford University Press, 1941). ↑
-
Aaron Good, “American Exception: Hegemony and the Dissimulation of the State,” Administration and Society, April 17, 2015, 23. ↑
-
Good, “American Exception: Hegemony and the Tripartite State,” 277. ↑
-
Carl Schmitt, Political Theology, trans. George Schwab (Chicago: University of Chicago Press, 1985), 5. ↑
-
Schmitt, Political Theology, 6. ↑
-
Good, “American Exception: Hegemony and the Dissimulation of the State.” ↑
-
Peter Dale Scott, The Road to 9/11: Wealth, Empire, and the Future of America (Berkeley, CA: University of California Press, 2007), 183-184. ↑
-
Scott, The American Deep State, 121. ↑
-
Scott, The Road to 9/11, 47. ↑
-
Stephen Kinzer, “From Mind Control to Murder? How a Deadly Fall Revealed the CIA’s Darkest Secrets,” The Guardian, September 6, 2019, https://www.theguardian.com/us-news/2019/sep/06/from-mind-control-to-murder-how-a-deadly-fall-revealed-the-cias-darkest-secrets. ↑
-
Tamsin Shaw, “The Bitter Secret of ‘Wormwood,’” The New York Review of Books, January 18, 2018, https://www.nybooks.com/daily/2018/01/18/the-bitter-secret-of-wormwood/. ↑
-
John M. Crewdson, “Hunt Says CIA Had Assassin Unit,” The New York Times, December 26, 1975, https://www.nytimes.com/1975/12/26/archives/hunt-says-cia-had-assassin-unit-watergate-figure-tells-of-small.html. ↑
-
Good, “American Exception” 201-202. ↑
-
Scott, The Road to 9/11, 23. ↑
-
Scott, The Road to 9/11, 186-187. ↑
-
Scott, The Road to 9/11, Chapters 13 and 14. ↑
-
Scott, The American Deep State, 40. ↑
-
Other notable examples evincing elements of these perspectives include Henry Luce, “The American Century,” Life, February 17, 1941, https://books.google.com/books?id=I0kEAAAAMBAJ&printsec=frontcover#v=onepage&q&f=false; George Kennan, “The Long Telegram” (Moscow, 1946), https://nsarchive2.gwu.edu/coldwar/documents/episode-1/kennan.htm; “NSC 68: United States Objectives and Programs for National Security” (Washington, D.C., April 14, 1950), https://www.mtholyoke.edu/acad/intrel/nsc-68/nsc68-1.htm; “FY 94-99 Defense Planning Guidance (Draft)” (Washington, D.C., 1992), https://nsarchive2.gwu.edu/nukevault/ebb245/doc03_extract_nytedit.pdf; Thomas Donnelly, “Rebuilding America’s Defenses: Strategy, Forces and Resources For a New Century”; Anonymous, “The Longer Telegram: Toward A New American China Strategy,” Atlantic Council Strategy Papers (Washington, D.C., 2021), https://www.atlanticcouncil.org/wp-content/uploads/2021/01/The-Longer-Telegram-Toward-A-New-American-China-Strategy.pdf. ↑
-
See Iran, Guatemala, Congo, Brazil, Indonesia, Chile, etc…. ↑
-
We borrow this term from our friend Daniel Ellsberg. ↑
-
Scott, The American Deep State, 9. ↑
-
Evan Thomas, Newsweek, December 30, 2001, https://www.newsweek.com/day-changed-america-148319. I argue in The Road to 9/11 that Cheney may have entered the PEOC twice, the second time after making an important COG phone call to Bush (Scott, The Road to 9/11, 200-03, 221-22). ↑
-
For Mineta’s allegations and the Commission’s handling of them, see Scott, The Road to 9/11, 199-206. ↑
-
Enough is known about the training of the alleged Arab hijackers to assert that they never approached the level of competence needed to fly a jet airliner into a specific building. ↑
-
In the case of 9/11, I suspect there also may have been a third dark force with a third and far more lethal goal, to bring the Twin Towers, in a yet another piggy-backed plot, to the ground for insurance purposes. In this essay I will not discuss the possible third plot. ↑
-
For an overview of COG involvement in previous structural deep events, see Scott, The American Deep State, 109-20. ↑
-
In 1994, Tim Weiner reported in The New York Times that what he called “The Doomsday Project” – the search for “ways to keep the Government running after a sustained nuclear attack on Washington” – had “less than six months to live.” [See Tim Weiner, “Pentagon Book For Doomsday Is to Be Closed,” The New York Times, April 18, 1994, https://www.nytimes.com/1994/04/18/us/pentagon-book-for-doomsday-is-to-be-closed.html.] Weiner’s language was technically correct, but also very misleading. In fact, COG planning now simply continued with a new target: terrorism. On the basis of Weiner’s article, the first two books to discuss COG planning, by James Bamford and James Mann, both reported that COG planning had been abandoned. Tim Shorrock in 2008 repeated that “the COG program was abandoned during the Clinton administration,” and Shirley Anne Warshaw in 2009 wrote that “the Clinton administration … shut down the super-secret Project.” But on this specific point, all these otherwise excellent and well-informed authors were wrong. ↑
-
Excerpt from August 19, 1961, memorandum to National Security Adviser McGeorge Bundy from
Presidential Assistant Frederick G. Dutton, http://historynewsnetwork.org/blog/27864. ↑
-
Matthew L. Conaty, “The Atomic Midwife: The Eisenhower Administration’s Continuity-of-Government Plans and the Legacy of ‘Constitutional Dictatorship,’” Rutgers Law Review, Vol. 62, No. 3, Spring 2010, 7-8. ↑
-
Executive Order 11490, October 28, 1969; Executive Order 11921, “Emergency Preparedness Functions,” June 11, 1976, Federal Register, vol. 41, no. 116 (Washington, D.C.: Government Printing Office (GPO), June 15, 1976, pp. 294-300, quoted in Diana Reynolds, “FEMA and the NSC: The Rise of the National Security State,” Covert Action Information Bulletin, 53, 1990, 33. ↑
-
Howard Ruff, How to Prosper during the Coming Bad Years (New York: Warner Books, 1979), 150. ↑
-
Michel Crozier, Samuel P. Huntington, and Joji Watanuki, The Crisis of Democracy, Trilateral Commission Report, 113. ↑
-
The Carter administration should perhaps be remembered as the Trilateral Administration: The Trilaterals in it included President Carter and Vice President Mondale, National Security Adviser Brzezinski, Secretary of State Cyrus Vance, Secretary of Defense Harold Brown, and Secretary of the Treasury Michael Blumenthal (Jay Peterzell, “The Trilateral Commission and the Carter Administration,” Economic and Political Weekly, Vol. 12, No. 51 December 17, 1977,, 2097-2104). ↑
-
After Carter’s defeat in 1980, Huntington continued to serve as a member of FEMA’s Advisory Board. Brzezinski rejoined him in government as a senior consultant to the George H.W. Bush administration. ↑
-
Charles Perrow, “Using Organizations: The Case of FEMA,” Items, Social Science Research Council, June 11, 2006, https://items.ssrc.org/understanding-katrina/using-organizations-the-case-of-fema/. ↑
-
Ibid. ↑
-
Perrow, “Using Organizations.” ↑
-
When North had to send emergency instructions for arms delivery to the U.S. Embassy in Lisbon, instructions that directly contravened the embargo prohibiting such sales, he used the Flashboard network to avoid alerting the Ambassador and other unwitting personnel. The records of the President’s Special Review Board (Tower Board) set up under Reagan to review Iran-Contra, are stored at the Reagan Library. In Box 93199 is a folder, “Flashboard SRB 1178.” I hope some younger scholar will FOIA for this folder and analyze it. ↑
-
Alfonso Chardy, Miami Herald, July 5, 1987. In October 1984 Jack Anderson also reported that FEMA’s plans would “suspend the Constitution and the Bill of Rights, effectively eliminate private property, abolish free enterprise, and generally clamp Americans in a totalitarian vise.” ↑
-
The New York Times, July 14, 1987. ↑
-
“For the first time in history… contingency plans for the continuity of government had been implemented” (9/11 Commission Report, 326, cf. 38). Many have found this crucial but underreported fact hard to believe. The first two print reviews of The Road to 9/11, both favorable and intelligently written, both reported that I speculated that COG had been imposed on 9/11. ↑
-
Barton Gellman and Susan Schmidt, “Shadow Government Is at Work in Secret,” The Washington Post, March 1, 2002, https://www.washingtonpost.com/archive/politics/2002/03/01/shadow-government-is-at-work-in-secret/247be9d2-4409-4f10-8923-54deacf46bfd/. ↑
-
Shirley Anne Warshaw, The Co-Presidency of Bush and Cheney (Stanford, CA: Stanford Politics and Policy, 2009), 164-65. ↑
-
Amy Goldstein and Juliet Eilperin, “Congress Not Advised of Shadow Government,” The Washington Post, March 2, 2002; cf. “‘Shadow Government’ News To Congress.” CBS News, March 2, 2002, https://web.archive.org/web/20110905080451/http://www.cbsnews.com/stories/2002/03/01/attack/main502530.shtml: “Key congressional leaders say they didn’t know President Bush had established a ‘shadow government,’ moving dozens of senior civilian managers to secret underground locations outside Washington to ensure that the federal government could survive a devastating terrorist attack on the nation’s capital, The Washington Post says in its Saturday editions. Senate Majority Leader Thomas A. Daschle (D-S.D.) told the Post he had not been informed by the White House about the role, location or even the existence of the shadow government that the administration began to deploy the morning of the Sept. 11 hijackings.” ↑
-
In the early stages of COG planning, provisions were made for the post-nuclear survival of Congress at GREENBRIER, an underground redoubt under a West Virginia hotel constructed in 1959-62. It was dropped from COG planning in the 1980s and is now a tourist site. ↑
-
Barton Gellman, Angler: The Cheney Vice Presidency (New York: Penguin Press, 2008), 133–35. Yoo has denied this, assuring me that on 9/11 he had no contact with either Cheney or Addington. I believe Gellman. ↑
-
Attorney General Ashcroft, in Chicago that morning, had been told by Rice with Cheney in the PEOC on his return to join his deputy, Larry Thompson, and his assistant, David Ayres, who had already been sent out of Washington to a classified COG site. Because of traffic conditions, Ashcroft was ultimately redirected that afternoon to the FBI Crisis Management Center. See John Ashcroft, Never Again: Securing America and Restoring Justice (New York: Center Street, 2006). Yoo’s eventual boss at the OLC, Jay Bybee, had not yet been appointed. Bybee’s position, as assistant attorney general for the Office of Legal Counsel, required Senate confirmation. His name had been submitted to the Senate on September 4, 2011, one week before 9/11. ↑
-
Gellman, Angler, 191. ↑
-
The provisions of Executive Order 12656 of Nov. 18, 1988, appear at 53 FR 47491, 3 CFR, 1988 Comp., p. 585, https://www.archives.gov/federal-register/codification/executive-order/12656.html. The Washington Post (March 1, 2002) later claimed, falsely, that Executive Order 12656 dealt only with “a nuclear attack.” Earlier there was a similar misrepresentation in the New York Times (November 18, 1991). ↑
-
Notice on the Continuation of the National Emergency with Respect to Certain Terrorist Attacks, The White House, September 09, 2021, https://www.whitehouse.gov/briefing-room/presidential-actions/2021/09/09/notice-on-the-continuation-of-the-national-emergency-with-respect-to-certain-terrorist-attacks/. We can expect similar action this month to renew EO 13224, the authority under which he is withholding reserves of the Afghan Government from the Taliban. ↑
-
One Congressman explained to a constituent that the provisions of the National Emergencies Act have now been rendered inoperative by COG. If true, this would seem to justify Chardy’s description of COG as a suspension of the Constitution. ↑
-
Federal Emergency Management Agency, Federal Continuity Directive 1, link. NSPD-51 also nullified PDD 67, Richard Clarke’s COG directive of a decade earlier; and it referred to new “classified Continuity Annexes” which shall “be protected from unauthorized disclosure.” ↑
-
Scott, The American Deep State, 40. ↑
-
Natalie Andrews, “Congressional Leaders Evacuated to DC’s Fort McNair,” Wall Street Journal, January 6, 2021, at 3:46 p.m. ET, https://www.wsj.com/livecoverage/biden-trump-electoral-college-certification-congress/card/mnrsBQyQbVtGvXOlg6Ov. ↑
-
Mark Preston, “Senate ‘Meets’ at Fort McNair: Hundreds Participate in Disaster Drill,” Roll Call, January 20, 2004, https://www.rollcall.com/2004/01/20/senate-meets-at-fort-mcnair/. ↑
-
Carol Leonnig and Philip Rucker, I Alone Can Fix It: Donald J. Trump’s Catastrophic Final Year (New York: Penguin Press, 2021), 181. On July 15, 2021, one week before the book’s release, an advance story read: “The top Democrat and Republican, as well as fellow leaders Chuck Schumer and Kevin McCarthy, were transported from the Capitol to Fort McNair, an Army post in southwest Washington, during the chaos, the book says” (Oma Seddiq, “Pence refused to leave the Capitol during the January 6 riot despite Secret Service agents urging him to evacuate, saying, ‘I’m not getting in the car’: book,” Yahoo!Money, July 15, 2021, https://money.yahoo.com/mike-pence-refused-leave-capitol-205925651.html). But this exact passage does not occur in the book; it is only implied. ↑
-
Leonnig and Rucker, I Alone Can Fix It, 466-67; cf. Woodward and Costa, Peril, 244. ↑
-
Victoria Bekiempis, Guardian, December 31, 2020, https://www.theguardian.com/us-news/2020/dec/31/joe-biden-secret-service-team-trump-loyalty. ↑
-
Rebecca Shabad, “D.C. National Guard chief: Pentagon took 3 hours to greenlight troops during Capitol assault,” NBC News, March 3, 2021, https://www.nbcnews.com/politics/congress/national-security-officials-testify-about-jan-6-attack-capitol-joint-n1259434. ↑
-
Neil MacFarquhar, “Defendant in Plot to Kidnap Michigan Governor Is Sentenced to Six Years,” New York Times, August 25, 2021, https://www.nytimes.com/2021/08/25/us/gretchen-whitmer-kidnapping-plot-michigan.html. ↑
-
Ken Bensinger, “Watching the Watchmen,” BuzzFeed News, July 20, 2021, https://www.buzzfeednews.com/article/kenbensinger/michigan-kidnapping-gretchen-whitmer-fbi-informant. ↑
-
“Man charged in Capitol riot worked for FBI, lawyer says,” AP, February 9, 2021, https://www.nbcnews.com/news/us-news/man-charged-capitol-riot-worked-fbi-lawyer-says-n1257121: “Thomas Caldwell, who authorities believe holds a leadership role in the extremist group, worked as a section chief for the FBI from 2009 to 2010 after retiring from the Navy, his lawyer, Thomas Plofchan, wrote in a motion urging the judge to release him from jail while he awaits trial. The defense said Caldwell, who has denied being part of the Oath Keepers, has held a top-secret security clearance since 1979, which required multiple special background investigations, according to Plofchan. Caldwell also ran a consulting firm that did classified work for the U.S. government, the lawyer said.” ↑
-
“639 people have been charged in the Capitol insurrection so far. This searchable table shows them all,” Insider, August 30, 2021, https://www.insider.com/all-the-us-capitol-pro-trump-riot-arrests-charges-names-2021-1. ↑
-
Jaclyn Diaz and Rachel Treisman, “Members Of Right-Wing Militias, Extremist Groups Are Latest Charged In Capitol Siege,” NPR, January 19, 2021, https://www.npr.org/sections/insurrection-at-the-capitol/2021/01/19/958240531/members-of-right-wing-militias-extremist-groups-are-latest-charged-in-capitol-si: “People allegedly affiliated with organizations such as The Three Percenters, The Oath Keepers, Proud Boys, Texas Freedom Force, and other self-described Nazis and white supremacists were among the mob that stormed the U.S. Capitol building, according to federal investigators.” ↑
-
Leonnig and Rucker, I Alone Can Fix It, 481; cf. 473. ↑
-
Jen Judson and Aaron Mehta, “Army secretary McCarthy could be asked to stay in Biden administration,” Defense News, December 9, 2020, https://www.defensenews.com/land/2020/12/09/mccarthy-could-serve-as-interim-army-secretary-in-biden-administration/. In fact, McCarthy resigned on January 20. ↑
-
Peter Dale Scott, Deep Politics and the Death of JFK (Berkeley: University of California Press, 1993), 280; citing Warren Report, 25-26, 463. ↑
-
9/11 Report, 555n9: “The 9/11 crisis tested the U.S. government’s plans and capabilities to ensure the continuity of constitutional government and the continuity of government operations. We did not investigate this topic, except as needed to understand the activities and communications of key officials on 9/11. The Chair, Vice Chair, and senior staff were briefed on the general nature and implementation of these continuity plans.” In other words, the 9/11 Commission itself was NOT briefed. ↑
-
I discuss this utilization of Structural Deep Events as part of a strategy of tension in Peter Dale Scott, “Systemic Destabilization in Recent American History: 9/11, the JFK Assassination, and the Oklahoma City Bombing as a Strategy of Tension,” The Asia-Pacific Journal, September 22, 2012, https://apjjf.org/2012/10/39/Peter-Dale-Scott/3835/article.html. If my prediction holds true, then January 6 should be seen as having contributed to a prolongation of this strategy of tension. ↑
CovertAction Magazine is made possible by subscriptions, orders and donations from readers like you.
Blow the Whistle on U.S. Imperialism
Click the whistle and donate
When you donate to CovertAction Magazine, you are supporting investigative journalism. Your contributions go directly to supporting the development, production, editing, and dissemination of the Magazine.
CovertAction Magazine does not receive corporate or government sponsorship. Yet, we hold a steadfast commitment to providing compensation for writers, editorial and technical support. Your support helps facilitate this compensation as well as increase the caliber of this work.
Please make a donation by clicking on the donate logo above and enter the amount and your credit or debit card information.
CovertAction Institute, Inc. (CAI) is a 501(c)(3) non-profit organization and your gift is tax-deductible for federal income purposes. CAI’s tax-exempt ID number is 87-2461683.
We sincerely thank you for your support.
Disclaimer: The contents of this article are the sole responsibility of the author(s). CovertAction Institute, Inc. (CAI), including its Board of Directors (BD), Editorial Board (EB), Advisory Board (AB), staff, volunteers and its projects (including CovertAction Magazine) are not responsible for any inaccurate or incorrect statement in this article. This article also does not necessarily represent the views the BD, the EB, the AB, staff, volunteers, or any members of its projects.
Differing viewpoints: CAM publishes articles with differing viewpoints in an effort to nurture vibrant debate and thoughtful critical analysis. Feel free to comment on the articles in the comment section and/or send your letters to the Editors, which we will publish in the Letters column.
Copyrighted Material: This web site may contain copyrighted material the use of which has not always been specifically authorized by the copyright owner. As a not-for-profit charitable organization incorporated in the State of New York, we are making such material available in an effort to advance the understanding of humanity’s problems and hopefully to help find solutions for those problems. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. You can read more about ‘fair use’ and US Copyright Law at the Legal Information Institute of Cornell Law School.
Republishing: CovertAction Magazine (CAM) grants permission to cross-post CAM articles on not-for-profit community internet sites as long as the source is acknowledged together with a hyperlink to the original CovertAction Magazine article. Also, kindly let us know at info@CovertActionMagazine.com. For publication of CAM articles in print or other forms including commercial internet sites, contact: info@CovertActionMagazine.com.
By using this site, you agree to these terms above.
About the Author

Aaron Good is Editor at Large for CovertAction Magazine.
His revised doctoral dissertation, American Exception: Empire and the Deep State, is to be published by Skyhorse in the spring of 2022.
You can follow Aaron on Twitter: @Aaron_Good_
Ben Howard is an independent researcher.
He lives in Massachusetts with his wife and daughter.
You can follow Ben on Twitter: @housetrotter.
Peter Dale Scott is a former Canadian diplomat and poet.
Peter has written many important books on the CIA and the so-called “deep state,” including Deep Politics and the Death of JFK (University of California, 1993); The War Conspiracy, rev ed. (Skyhorse, 2008); The Road to 9/11 (University of California, 2007), American War Machine (Rowman & Littlefield, 2010) and The American Deep State (Rowman & Littlefield, 2017).
You can follow Peter’s work at: peterdalescott.net.









I find it interseting how little interest the P2OG have attracted.
“Proactive, Preemptive Operations Group (P2OG, PPOG) is a proposed U.S. intelligence agency that would employ “black world” (black operations) tactics.
The Defense Science Board (DSB) conducted a 2002 “DSB Summer Study on Special Operations and Joint Forces in Support of Countering Terrorism.”[1] Excerpts from that study, dated August 16, 2002, recommend the creation of a super-Intelligence Support Activity, an organization it dubs the Proactive, Preemptive Operations Group (P2OG), to bring together CIA and military covert action, information warfare, intelligence and cover and deception.[2] For example, the Pentagon and CIA would work together to increase human intelligence (HUMINT), forward/operational presence and to deploy new clandestine technical capabilities.[3] Concerning the tactics P2OG would use,
Among other things, this body would launch secret operations aimed at “stimulating reactions” among terrorists and states possessing weapons of mass destruction—that is, for instance, prodding terrorist cells into action and exposing themselves to “quick-response” attacks by U.S. forces.
Such tactics would hold “states/sub-state actors accountable” and “signal to harboring states that their sovereignty will be at risk”, the briefing paper declares.[2]” Wkipedia
John Pilger have written about it, but I would very much se what Covert Action Magazin could dig up on this.
http://johnpilger.com/articles/two-years-ago-a-project-set-up-by-the-men-who-now-surround-george-w-bush-said-what-america-needed-was-a-new-pearl-harbor-its-published-aims-have-come-alarmingly-true?fbclid=IwAR28xCJUnkevpF28-T-ZbPbZX029DpArs3SK7bQMYJgLvNhlAMLIPc3HMLg
[…] CovertAction Magazine (Aaron Good, Ben Howard and Peter Dale Scott) – Stepping out of the Shadow of 9/11: Start by Ending the Post-9/11 States of Emergency […]
[…] [by Peter Dale Scott | via CovertAction Magazine | September 27, 2021] […]
BRIEFING ROOM
Notice on the Continuation of the National Emergency with Respect to Certain Terrorist Attacks
SEPTEMBER 09, 2021
•
PRESIDENTIAL ACTIONS
Consistent with section 202(d) of the National Emergencies Act, 50 U.S.C. 1622(d), I am continuing for 1 year the national emergency previously declared on September 14, 2001, in Proclamation 7463, with respect to the terrorist attacks of September 11, 2001, and the continuing and immediate threat of further attacks on the United States.
Because the terrorist threat continues, the national emergency declared on September 14, 2001, and the powers and authorities adopted to deal with that emergency must continue in effect beyond September 14, 2021. Therefore, I am continuing in effect for an additional year the national emergency that was declared on September 14, 2001, with respect to the terrorist threat.
This notice shall be published in the Federal Register and transmitted to the Congress.
JOSEPH R. BIDEN JR.
THE WHITE HOUSE,
September 9, 2021
[…] Public support for such a draconian bill requires historical ignorance of state involvement in terrorist false flags. Consider the terrorism campaign of Operation Gladio, originally blamed on communists but found by the Italian parliament and European Commission to have been carried out by the CIA, Italian intelligence, and fascist elements. As terrorist Vincenzo Vinciguerra testified to an outraged Parliament: “the knowledge should now be clear that there existed a real live structure, occult and hidden, with the capacity of giving strategic direction to the outrages.” As scholar Daniele Ganser has noted, this “occult and hidden” structure gives an illustration of how a small clique within the state can carry out covert crimes while the majority of officials and elected representatives remain unaware. Another example of this dynamic can be seen by Sen. Tom Daschle’s claim that “none of us knew about the secret government” in reference to the Continuity of Government program initiated after 9/11 that may still be ongoing today. […]
[…] profundo como, por ejemplo, el 11 de septiembre es “una especie de encubrimiento” [1].Las normas burguesas típicamente evitan que estas personas ahonden demasiado en lo que se está […]
[…] Public support for such a draconian bill requires historical ignorance of state involvement in terrorist false flags. Consider the terrorism campaign of Operation Gladio, originally blamed on communists but found by the Italian parliament and European Commission to have been carried out by the CIA, Italian intelligence, and fascist elements. As terrorist Vincenzo Vinciguerra testified to an outraged Parliament: “the knowledge should now be clear that there existed a real live structure, occult and hidden, with the capacity of giving strategic direction to the outrages.” As scholar Daniele Ganser has noted, this “occult and hidden” structure gives an illustration of how a small clique within the state can carry out covert crimes while the majority of officials and elected representatives remain unaware. Another example of this dynamic can be seen by Sen. Tom Daschle’s claim that “none of us knew about the secret government” in reference to the Continuity of Government program initiated after 9/11 that may still be ongoing today. […]
https://www.youtube.com/watch?v=_FVAzn1Yuz8
I love these 9/11 articles! I thought I knew a thing or two about the subject but wow! I don’t know jack!
[…] Stepping out of the Shadow of 9/11: Start by Ending the Post-9/11 States of Emergency […]
I knew it was a false flag on that day of 911 but
missed 1-6 which makes perfect sense and explains a lot of behavior that otherwise doesn’t equate like failure to impeach the movie and sequel and the current son of Zbignew non impeachy
The front government is itself not hardly accountable so of course the shadows are on fire
I had my mic turned off trying to speak publically about 9-11 at s f taxi commission
Then sKamellla put me in jail …. Oh well
Yep something smells bad in the city state
I keep thinking about that stupid song ending of 2112 ….”we have assumed control”
Like Biden overides and mandates needle rape and face diapers false flag
Mandates for total control so we don’t have to think much , and anyway, there isn’t really much to think about
I think of Julian Assange also refused to agree with his own removal
But we have no real way to stop any of this as the 1st amendment has long ago been removed
From practice
If one can’t speak of any truthful matters then all that remains are false flags
The whole article has been like climbing a mountain and seeing History in 360º. Thank you for what I have learned
Sep 27, 2021
WATCH: COVID19/11 – CJ Hopkins
COVID19/11: Narratives Intertwined is OffG’s new series of short interviews with prominent voices in the alternate media, vocal Covid sceptics and leading figures in the 9/11 truth movement. The series…
Read more…
This is the latest COG operation, COVID, and so many are so timid to make the connection, but not Off Guardian