
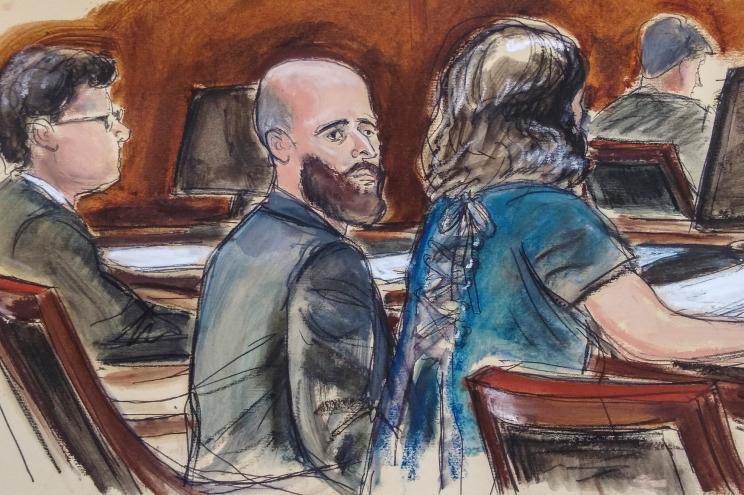
A federal jury in New York last month convicted former CIA officer Joshua Schulte on nine felony counts under the Espionage Act for providing information to WikiLeaks that became known as Vault 7.
Schulte has consistently denied that he was the source of the information.
Two years ago, he was convicted on two of the original 11 charges, while the jury hung on the remaining nine.
The most recent trial, in which Schulte represented himself, was on those nine counts, and he now faces as many as 80 years in prison. Schulte is yet to be tried on state child pornography charges.
Prosecutors had literally no evidence that Schulte had taken the data from the CIA and transferred it to WikiLeaks.
But they contended that he was a computer genius who is so brilliant that he was able to cover his tracks.
They alleged that he leaked the information because he was a disgruntled former CIA employee who hated his boss, couldn’t get along with his coworkers, and sought revenge against the Agency.
That was enough for the jury.
CIA Deputy Director for Digital Innovation Sean Roche called the Vault 7 leak “a digital Pearl Harbor.”
Chief prosecutor Damian Williams said the revelations were “one of the most brazen and damaging acts of espionage in American history.” And Vice magazine said it was “the worst leak of CIA information ever.”

The CIA leadership apparently thought the leak was so damaging that then-CIA Director Mike Pompeo ordered the Agency to come up with a plan to kidnap or to kill Julian Assange in London. One former Trump Administration national security official said that Pompeo and other senior CIA leaders, “were completely detached from reality because they were so embarrassed about Vault 7. They were seeing blood.”

All of the major media outlets reported on the finalization of Schulte’s case. What they haven’t reported on, though, is exactly what Schulte was accused of leaking in the first place.
What did we learn from Vault 7?
Vault 7 was a series of 24 collections of documents totaling hundreds of thousands of pages that included the most sophisticated computer hacking, surveillance, and cyberwarfare tools that the CIA ever developed.
WikiLeaks published the first tranche, called “Year Zero,” on March 7, 2017.
Just this first installment contained more information than all of that released by Edward Snowden and included vulnerabilities known to the CIA within web browsers, including Google Chrome, Microsoft Edge, Mozilla Firefox, and Opera and the operating systems of most of the world’s cellphones, including Apple’s iOS and Google’s Android.
The fact that the CIA knew about these vulnerabilities and didn’t inform the companies was a violation of a longstanding policy that the Agency claims to have that it would assist U.S. tech companies with their security if it learned of security weaknesses.
Instead, it exploited those problems in its digital operations. We have no idea if the Agency used these vulnerabilities to spy on Americans. Ashley Gorski, an American Civil Liberties Union staff attorney said at the time, “Our government should be working to help the companies patch vulnerabilities when they are discovered, not stockpile them.”

A second Vault 7 revelation came on March 23, 2017 and included accounts of CIA efforts to hack Apple’s iPhones and Mac computers.
Additional tranches were released every week or two until September 2017.
Their revelations included proof that the CIA was able to hack into cars’ computer systems and could take over control of the vehicle.
Was the purpose of this to force the vehicle off the road? Off a cliff? Into a tree? The CIA never commented.
Still other documents showed how CIA officers could take over an unsuspecting person’s smart TV and turn its speaker into a microphone to surreptitiously bug a room, even while the television appears to be turned off.
Yet other documents showed that the CIA was running digital operations against the National Security Agency (NSA). It is unclear whether this was done as an exercise between the two agencies or if it was something more sinister.
Other revelations were that the CIA had created a program to track documents transferred by would-be whistleblowers to media outlets (the program is called “Scribblers”), malware that can take over and control computers using the Microsoft Windows 10 operating system (called “Athena”), and malware that can be transferred from one “clean” computer to another through internal systems that are otherwise protected by anti-virus software (called “Pandemic”).
Schulte’s revelations were not limited to software. He also revealed a program called “HammerDrill,” that injects a trojan horse onto CDs and DVDs and then documents information on the discs for later transmission to the CIA.
An operation called “Dark Matter” revealed security vulnerabilities unique to Apple operating systems. And Schulte revealed that the CIA had compromised vulnerabilities in a huge range of Cisco Systems router models. Apple and Cisco spent untold millions of dollars to redesign their products and correct the security flaws.
Despite the fact that this was supposedly the worst data breach in the history of the CIA, Schulte and his revelations did not get much press play.
There are several likely reasons for this. First, Schulte claimed innocence. He insisted that he was not a whistleblower and he has maintained throughout his ordeal that he did not provide WikiLeaks with anything.
Second, the state of New York, simultaneously with the federal charges, charged Schulte with multiple counts of child pornography, which has given many of Schulte’s natural supporters pause.
Prosecutors maintained that they only discovered the pornography when they seized the computer hard drives in Schulte’s apartment while looking for Vault 7 information. Schulte’s defense to the child pornography charges will be that he considers himself to be a libertarian anarchist and that he set up a server to allow people unfettered “free speech,” something akin to the 4chan and 8chan servers.
He maintains that he has not “received” or “disseminated” any child pornography personally. However, when child pornographers saw that Schulte’s server supported “unfettered free speech,” they used it to trade illegal images and videos. Schulte is adamant that none of the pornography was his. His protestations likely won’t matter.
I’m of two minds on Joshua Schulte. On the one hand, the American people have a right to know what the government is doing in their name, especially if what the government is doing is illegal. On the other hand, Schulte is adamant that he is not the person who provided WikiLeaks with the information. Does that mean we walk away from Schulte and celebrate an anonymous whistleblower?
Either way, one of the things that I feel strongly about is the treatment that Schulte has endured.
He has been held in barbaric conditions over the past two years, kept in a literal cage in solitary confinement at the Metropolitan Correctional Center (MCC) in Brooklyn, New York.
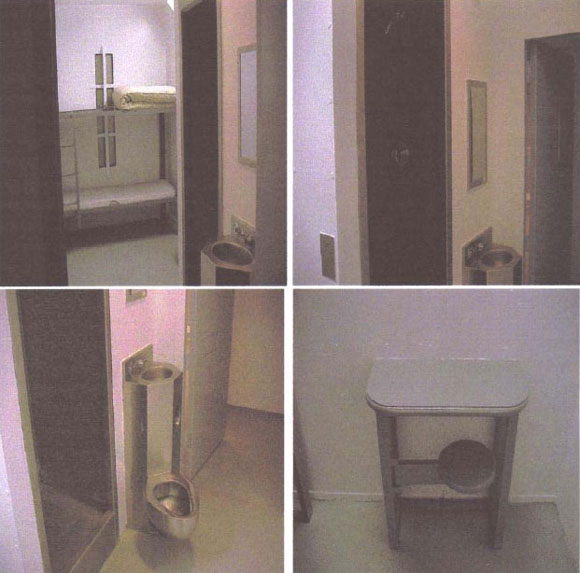
Now that he has been convicted, he’ll likely be placed in a Special Administrative Unit or a Communications Management Unit in a maximum-security or Supermax penitentiary.
The government will seek to cut him off from the rest of the world for as long as possible. That alone should be worth our interest and disgust.

CovertAction Magazine is made possible by subscriptions, orders and donations from readers like you.
Blow the Whistle on U.S. Imperialism
Click the whistle and donate
When you donate to CovertAction Magazine, you are supporting investigative journalism. Your contributions go directly to supporting the development, production, editing, and dissemination of the Magazine.
CovertAction Magazine does not receive corporate or government sponsorship. Yet, we hold a steadfast commitment to providing compensation for writers, editorial and technical support. Your support helps facilitate this compensation as well as increase the caliber of this work.
Please make a donation by clicking on the donate logo above and enter the amount and your credit or debit card information.
CovertAction Institute, Inc. (CAI) is a 501(c)(3) non-profit organization and your gift is tax-deductible for federal income purposes. CAI’s tax-exempt ID number is 87-2461683.
We sincerely thank you for your support.
Disclaimer: The contents of this article are the sole responsibility of the author(s). CovertAction Institute, Inc. (CAI), including its Board of Directors (BD), Editorial Board (EB), Advisory Board (AB), staff, volunteers and its projects (including CovertAction Magazine) are not responsible for any inaccurate or incorrect statement in this article. This article also does not necessarily represent the views the BD, the EB, the AB, staff, volunteers, or any members of its projects.
Differing viewpoints: CAM publishes articles with differing viewpoints in an effort to nurture vibrant debate and thoughtful critical analysis. Feel free to comment on the articles in the comment section and/or send your letters to the Editors, which we will publish in the Letters column.
Copyrighted Material: This web site may contain copyrighted material the use of which has not always been specifically authorized by the copyright owner. As a not-for-profit charitable organization incorporated in the State of New York, we are making such material available in an effort to advance the understanding of humanity’s problems and hopefully to help find solutions for those problems. We believe this constitutes a ‘fair use’ of any such copyrighted material as provided for in section 107 of the US Copyright Law. You can read more about ‘fair use’ and US Copyright Law at the Legal Information Institute of Cornell Law School.
Republishing: CovertAction Magazine (CAM) grants permission to cross-post CAM articles on not-for-profit community internet sites as long as the source is acknowledged together with a hyperlink to the original CovertAction Magazine article. Also, kindly let us know at info@CovertActionMagazine.com. For publication of CAM articles in print or other forms including commercial internet sites, contact: info@CovertActionMagazine.com.
By using this site, you agree to these terms above.
About the Author

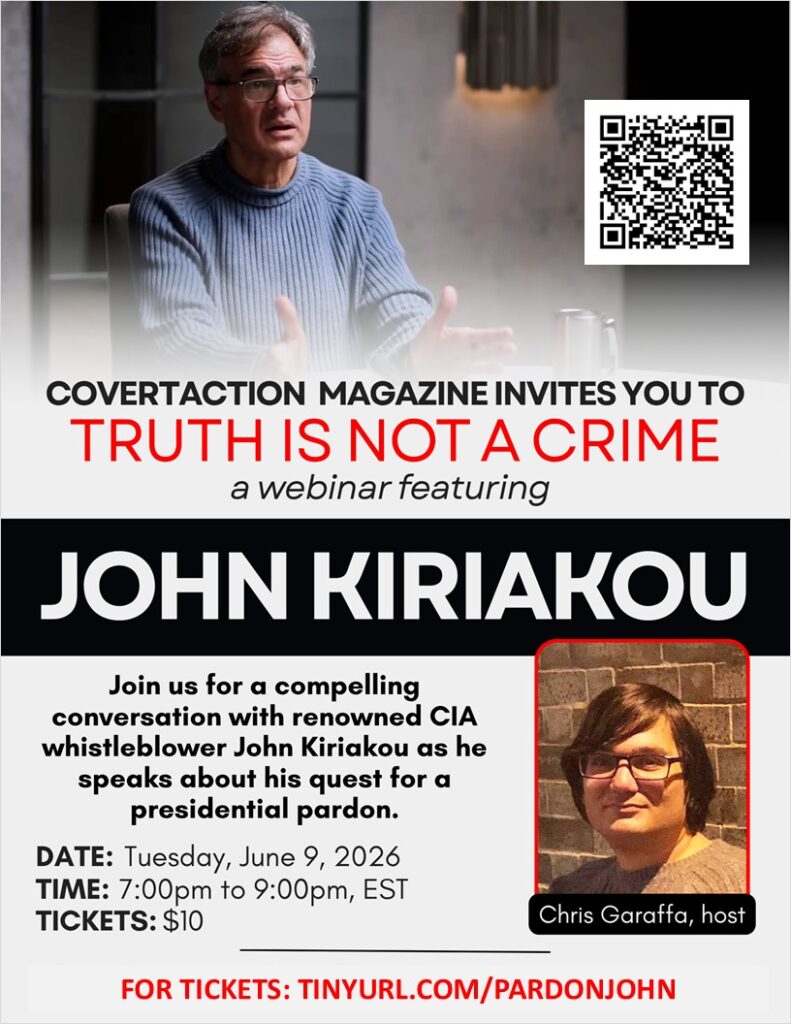
John Kiriakou was a CIA analyst and case officer from 1990 to 2004.
In December 2007, John was the first U.S. government official to confirm that waterboarding was used to interrogate al-Qaeda prisoners, a practice he described as torture.
Kiriakou was a former senior investigator for the Senate Foreign Relations Committee and a former counter-terrorism consultant. While employed with the CIA, he was involved in critical counter-terrorism missions following the terrorist attacks of September 11, 2001, but refused to be trained in so-called “enhanced interrogation techniques,” nor did he ever authorize or engage in such crimes.
After leaving the CIA, Kiriakou appeared on ABC News in an interview with Brian Ross, during which he became the first former CIA officer to confirm the existence of the CIA’s torture program. Kiriakou’s interview revealed that this practice was not just the result of a few rogue agents, but was official U.S. policy approved at the highest levels of the government.
Kiriakou is the sole CIA agent to go to jail in connection with the U.S. torture program, despite the fact that he never tortured anyone. Rather, he blew the whistle on this horrific wrongdoing.
John can be reached at: jkiriakou@mac.com.

I am a TI subject to DEW / Microwave attacks remotely for over 15 Years like thousands of other American Citizens all across USA. This is similar to Havana Syndrome on larger scale with many more symptoms. Please visit Targeted Justice and PACTS websites among other websites to know more about this illegal torture Program run via Military weapons.
[…] [7] https://covertactionmagazine.com/2022/08/16/former-cia-officer-joshua-schulte-faces-as-many-as-80-ye… […]
[…] [7] https://covertactionmagazine.com/2022/08/16/former-cia-officer-joshua-schulte-faces-as-many-as-80-ye… […]
[…] 12) Former CIA Officer Joshua Schulte Faces as Many as 80 Years in Prison After Being Convicted For Providing Information to WikiLeaks https://covertactionmagazine.com/2022/08/16/former-cia-officer-joshua-schulte-faces-as-many-as-80-ye… […]
[…] https://covertactionmagazine.com/2022/08/16/former-cia-officer-joshua-schulte-faces-as-manyas-80-yea… […]
[…] [7] https://covertactionmagazine.com/2022/08/16/former-cia-officer-joshua-schulte-faces-as-many-as-80-ye… […]
Thank you for Vault 7!
[…] Former CIA Officer Joshua Schulte Faces as Many as 80 Years in Prison After Being Convicted For Providing Information to WikiLeaks https://covertactionmagazine.com/2022/08/16/former-cia-officer-joshua-schulte-faces-as-many-as-80-ye… […]
Read these by Robert Duncan, who worked for the CIA and NSA in their Tech/Neuroweapons Depts., and info how easy technology gets for hacking: “The Matrix Deciphered”; “Project:Soul Catcher, Vol 2.” Conversely, read about #OrganizedContractStalking
Crushing irony! The cumulative crimes of the CIA deserve billions of years of prison time (and a lot of executions). Yet the man who is punished is the one who reveals a few of those crimes.
Land of the Free. Home of the Brave.
But the CIA are a bunch of cowards!
i’m an expat living in the NL…around 7 yrs, or so, ago, there was this big to do here about computer privacy…next thing i know, everywhere i go on my computer i’m being asked if i will allow cookies…
but here’s the point. i was at a cafe i frequented and they’re having this heated discussion about their information being ‘grabbed’…this really surprised me…
who(from an urban American city) would think OTHERwise?
people will do whatever they can to get what they want is a basic premise in my way of thinking…and i’m not saying this in any ‘angry’ way…i’m old. it seems to be the nature of the beast…there’s a hunger and it will be satisfied…
so the above ‘revelations’ about what the CIA might be doing with any tech they get their hands on(or help develop), and this is a serious question…i’m even going to tick the boxes to notify me about responses/new mails…are any of you REALly surprised by any of this?
i was a teenager when JFK was assassinated. and we still don’t really know who did it, regardless of Oliver Stone…what WON’T people with an agenda do to get what they want?
and this isn’t just the way it’s become recently…it seems to me it’s ALways been this way. anyone ever read any Shakespeare? or ‘Holy Books’?
that’s it.